Best 11 Privileged Access Management (PAM) Solutions For Enterprise (2026)
We reviewed the leading PAM platforms on vault architecture, session recording depth, and the just-in-time access controls that limit the blast radius when a privileged credential is compromised.
 Technical Review by
Laura Iannini
Technical Review by
Laura Iannini
Quick Summary
Privileged Access Management (PAM) solutions control the highest-value accounts in any environment — admin credentials, service accounts, and elevated privileges — through vaulting, session monitoring, and just-in-time access. Privileged account compromise gives attackers the access needed to move laterally and cause maximum damage; it is the primary target in most advanced attacks. We reviewed the top platforms and found JumpCloud, ThreatLocker Elevation Control, and One Identity Safeguard to be the strongest on vault architecture and session control depth.

Privileged accounts are the keys to your infrastructure. Admin credentials, service accounts, root access, API keys. When they get compromised, attackers skip the perimeter entirely and move straight to your most sensitive systems.
The challenge is that most organizations still manage privileged access manually. Shared admin passwords in spreadsheets, standing privileges that never expire, service accounts nobody remembers creating. Every one of those is a breach waiting to happen. Regulatory pressure makes it worse. Auditors want proof of who accessed what, when, and why.
We evaluated 11 privileged access management platforms across credential vaulting, session monitoring, just-in-time access, automated rotation, and threat detection capabilities. We reviewed customer feedback from regulated industries, enterprise IT, and mid-market deployments to understand where these platforms deliver real value and where complexity becomes the enemy of security. This guide gives you the decision framework to match the right PAM solution to your infrastructure, compliance requirements, and team capacity.
Our Recommendations
We evaluated these platforms on architecture, ease of deployment, and operational workflow impact. Each addresses different privilege management and monitoring requirements.
- Best For Unified Directory and Privilege Management: JumpCloud unifies directory services, SSO, device management, and PAM on single cross-platform console supporting Mac, Windows, and Linux with zero-trust authentication and simplified privilege workflows.
- Best For Application-Based Privilege Elevation: ThreatLocker grants temporary escalation based on application execution with kernel-level protection preventing unauthorized privilege acquisition.
- Best For Session Recording and Approval Workflows: One Identity Safeguard, BeyondTrust delivers session recording with approval workflows while unified identity and access management provides centralized control.
- Best For Hardware Security Keys and MFA: Keeper Security KeeperPAM, Yubico secures privileged access through hardware security keys with built-in FIDO2 phishing resistance.
- Best For Automated Privileged Account Management: ARCON|PAM, Delinea automates privileged account discovery and password rotation with session recording of administrative access.
JumpCloud is a unified identity, access, and device management platform that includes privileged access controls alongside MFA, SSO, and endpoint management. We think the value here is consolidation: instead of running separate tools for identity, PAM, and device management, JumpCloud handles all three from one console. It integrates with Azure AD and Google Workspace, or runs standalone.
JumpCloud Key Features
JumpCloud Go replaces password logins with device-verified biometric authentication using Touch ID or Windows Hello. The PAM module covers privileged credential management, SSH key management, real-time session monitoring with recording, and brute force alerting. Conditional access policies let you build rules around device posture, location, and user attributes. The secure browser-in-browser feature runs monitored sessions that block data downloads and strip extensions, which is practical for controlling third-party access. Device management spans Mac, Windows, Linux, iOS, and Android from the same console.
What Customers Say
Users consistently praise the single-console approach for cutting operational overhead across identity, access, and device policies. SSO access to cloud platforms like AWS and GCP gets credit for simplifying daily workflows. Some users report that the bulk upload feature lacks complete field support, pushing some tasks back to PowerShell. Device-level restrictions apply to all accounts on a machine rather than individual users.
Our Take
We think JumpCloud fits growing organizations that want identity, PAM, and device management in one place without the complexity of enterprise-grade standalone PAM. Pricing starts at $13/user/month for Core Directory. If you only need a single capability like session recording or credential vaulting, evaluate the bundled pricing against point solutions. JumpCloud returns the most value when your team uses multiple modules.
Strengths
- Combines MFA, SSO, PAM, and device management in one console
- JumpCloud Go replaces passwords with biometric authentication
- Cross-platform device management covers Mac, Windows, Linux, iOS, and Android
- Transparent per-user pricing from $13/user/month
Cautions
- Users report bulk account creation requires PowerShell for complete field data
- Bundled pricing can feel expensive for teams needing only one feature
ThreatLocker Elevation Control removes local admin rights and replaces them with policy-driven privilege elevation at the application level. We think this is a different approach to PAM than traditional credential vaulting: instead of managing who gets privileged accounts, ThreatLocker controls what specific applications can do with elevated privileges. It is part of ThreatLocker’s Unified Bundle alongside Allowlisting, Ringfencing, Network Control, and Storage Control.
ThreatLocker Elevation Control Key Features
The elevation model works at the application level rather than the user level. Administrators define which applications can run with elevated privileges and under what conditions, so end users never need local admin rights. Ringfencing restricts what elevated applications can access, preventing lateral movement even if a trusted application is compromised. The auto-learning mode builds a baseline of normal application behavior before enforcement, which reduces policy tuning during deployment. Approval workflows let users request temporary elevation for specific tasks, with full audit trails. ThreatLocker deploys through existing RMM tools, which matters for MSPs and IT teams managing distributed endpoints.
What Customers Say
The MSP community is where ThreatLocker shows up most consistently. Users credit the platform for eliminating the need to hand out local admin rights while keeping end-user friction low. The learning mode gets positive marks for reducing false positives during rollout. Some users mention that the initial policy configuration requires patience, and the volume of approval requests can be high during the first weeks of enforcement.
Our Take
We think ThreatLocker Elevation Control fits organizations, particularly MSPs and mid-market teams, that want to enforce least privilege at the endpoint without traditional PAM infrastructure. This is not a credential vault or session recorder; it is application-level privilege control. If you need full PAM with session recording and credential rotation, pair it with a dedicated PAM tool or look elsewhere. For removing local admin rights with minimal disruption, it delivers.
Strengths
- Removes local admin rights without disrupting end-user workflows
- Ringfencing prevents lateral movement from elevated applications
- Auto-learning mode reduces false positives during deployment
- Deploys through existing RMM tools
Cautions
- Not a traditional PAM platform; no credential vaulting or session recording
- Reviews note approval request volume can be high during initial enforcement
One Identity Safeguard is a PAM suite covering credential vaulting, session monitoring, and behavioral threat detection. It is part of the broader One Identity Fabric for unified identity security. One Identity was named a Visionary in the 2025 Gartner Magic Quadrant for PAM. We found the session analysis capabilities stand out: recordings are tamper-proof and fully searchable, and machine learning behavioral biometrics flag risky activity in real time rather than relying on static rules.
One Identity Safeguard Key Features
Behavioral biometrics analyze keystroke dynamics and mouse movement patterns to build a per-user baseline rather than matching against pre-defined rules. This moves session monitoring from passive recording into active threat detection. The password vault centralizes credential management with SSO, MFA, and automated rotation workflows. Access controls are policy-driven with customizable approval workflows for just-in-time and least-privilege scenarios. Cross-platform coverage extends PAM controls to Linux, Unix, and other non-Windows infrastructure, which is where many PAM platforms lose visibility.
What Customers Say
Users say Safeguard brought structure to environments previously running on manual processes and shared accounts. Customers cite intuitive UX and total cost of ownership as consistent strengths. Some reviews note administrative complexity during initial deployment, and implementation quality has varied across the broader One Identity suite.
Our Take
We think One Identity Safeguard fits large enterprises running multi-platform environments where identity governance and PAM need to work together. If your organization already uses the One Identity Fabric for IAM or IGA, adding Safeguard extends that investment. For smaller teams or straightforward environments, the Cloud PAM Essentials tier is worth evaluating as a lighter entry point.
Strengths
- Tamper-proof session recordings with ML behavioral analysis
- Per-user behavioral baselines instead of static detection rules
- Cross-platform coverage extends PAM to non-Windows infrastructure
- Policy-driven access controls with JIT and least-privilege workflows
Cautions
- Customers note administrative complexity during initial deployment
- Pricing only available directly from the vendor
KeeperPAM is a cloud-native privileged access management platform built on Keeper’s zero-knowledge encryption architecture. We think the key advantage is the unified approach: credential vaulting, session recording, secrets management, and remote access sit under one control plane with no on-premises infrastructure required. If your team already uses Keeper for password management, expanding to full PAM is a short step.
Keeper Security KeeperPAM Key Features
Zero-knowledge encryption means even Keeper cannot access your vault data. Keeper Connection Manager provides VPN-free access to internal and cloud resources, and remote browser isolation launches protected sessions without exposing credentials on endpoints. Automated password and secrets rotation runs alongside granular role-based permissions across cloud and on-premises environments. Session recording captures privileged activity for compliance audit trails. The Secrets Manager module handles API keys, database credentials, and other machine identities.
What Customers Say
Customers praise the autofill and password generation capabilities for reducing daily credential friction. The unified platform approach gets credit for replacing multiple point tools. Some users report autofill works inconsistently across certain sites and applications, and vault search requires more scrolling than expected to find specific records.
Our Take
We think KeeperPAM fits mid-sized to large organizations that want PAM without standing up on-premises appliances. The zero-knowledge architecture is a genuine differentiator for teams with strict data sovereignty requirements. If your environment has complex legacy infrastructure or needs highly customized session brokering, validate the fit first. For cloud-forward organizations, this is a strong option.
Strengths
- Zero-knowledge encryption protects credentials from all parties including Keeper
- VPN-free remote access eliminates a common deployment dependency
- Automated credential and secrets rotation closes a common attack path
- Extends naturally from Keeper password management
Cautions
- Users report autofill works inconsistently across certain sites
- Secrets Manager and advanced reporting carry additional cost
ARCON | Privileged Access Management

ARCON PAM manages the full privileged account lifecycle, from credential vaulting through session tracking to behavioral analytics. We think it is best suited for large regulated enterprises, particularly in banking and financial services, where audit compliance and standing access risk are the primary concerns. ARCON was named a Customers’ Choice in the 2025 Gartner Peer Insights Voice of the Customer for PAM.
ARCON PAM Key Features
The just-in-time access model grants privileges only when needed and revokes them automatically, cutting the standing access exposure that fuels credential-based attacks. MFA-secured vault access, dynamic password generation, and automated rotation reduce manual overhead on credential hygiene. ARCON Knight Analytics uses AI and machine learning to detect anomalous privileged identity behavior, building proactive detection rather than relying on static rules. Native SSO and OTP validation integrate with existing enterprise identity systems.
What Customers Say
The banking sector is where ARCON shows up most consistently. Large enterprise customers managing thousands of privileged accounts say the centralized control framework and audit reporting deliver real operational value. Some reviews note technical support resolutions run slow on complex issues, and initial setup requires significant time investment in large environments.
Our Take
We think ARCON PAM fits large regulated enterprises where audit compliance and standing access risk drive the PAM decision. If your environment runs thousands of privileged accounts across regulated infrastructure, the centralized framework handles that scale. If you need fast support turnaround or a quick deployment, set those expectations with the vendor upfront.
Strengths
- JIT access with automated revocation reduces standing privilege exposure
- AI-driven Knight Analytics detects anomalous privileged behavior
- MFA-secured vault with dynamic password generation and rotation
- Strong presence in banking and financial services
Cautions
- Reviews note technical support resolutions run slow on complex issues
- Pricing only available on request
BeyondTrust Privileged Remote Access

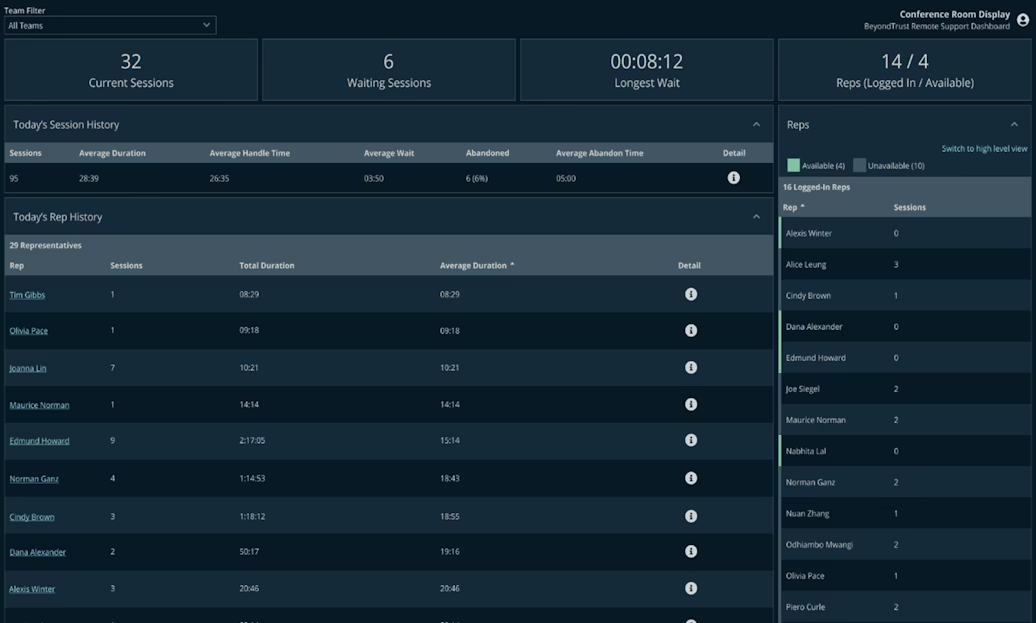
BeyondTrust Privileged Remote Access secures and manages privileged sessions for internal users, third-party vendors, and remote employees connecting to critical systems. We think the strongest use case is organizations that need to control vendor and contractor access to internal infrastructure without exposing VPN credentials or standing accounts. BeyondTrust was named a Leader in the 2024 Gartner Magic Quadrant for PAM.
BeyondTrust Privileged Remote Access Key Features
Vault-integrated session brokering injects credentials at connection time so users never see or handle passwords directly. Session monitoring records all privileged activity with full video playback and keystroke capture for audit and forensic review. Approval workflows enforce just-in-time access with time-limited sessions that auto-terminate. The platform supports RDP, SSH, VNC, and web-based sessions across cloud and on-premises infrastructure. Integration with BeyondTrust Password Safe centralizes credential management alongside session controls.
What Customers Say
Users highlight the session recording quality and the audit trail it produces for compliance reporting. The vendor access controls get particular credit from teams managing third-party contractors. Based on reviews, the interface can feel dated compared to cloud-native alternatives, and complex policy configurations require significant admin effort to maintain.
Our Take
We think BeyondTrust Privileged Remote Access fits mid-to-large enterprises that need strong control over remote privileged sessions, especially third-party vendor access. If your primary concern is who connects to what and what they do during those sessions, this addresses it directly. For organizations that need broader identity governance alongside PAM, evaluate the full BeyondTrust suite or consider platforms with native IGA integration.
Strengths
- Vault-integrated session brokering keeps credentials hidden from users
- Full session recording with video playback and keystroke capture
- Strong vendor and contractor access controls with time-limited sessions
- Supports RDP, SSH, VNC, and web-based sessions
Cautions
- Reviews mention the interface can feel dated compared to cloud-native tools
- Complex policy configurations require significant admin effort
Symantec Privileged Access Management

Symantec Privileged Access Management provides credential vaulting, session recording, and threat analytics for privileged accounts across hybrid infrastructure. Originally developed by CA Technologies, the product now operates under Broadcom’s Enterprise Security division following Broadcom’s acquisition of Symantec in 2019. We think this platform still serves organizations already invested in the Broadcom security ecosystem, but prospective buyers should evaluate the current product roadmap carefully.
Symantec PAM Key Features
The credential vault supports automated password rotation, check-in/check-out workflows, and policy-driven access controls. Session recording captures privileged activity across Windows, Linux, and Unix environments. Threat analytics monitor privileged sessions for anomalous behavior. The platform deploys as a hardened virtual appliance, which simplifies initial setup compared to multi-component installations. Integration with Symantec’s broader security stack, including Data Loss Prevention and endpoint tools, provides additional context for privileged activity monitoring.
What Customers Say
Users managing existing Symantec environments praise the integration with other Broadcom security products. The virtual appliance deployment model gets credit for reducing infrastructure complexity. Multiple customer reviews flag that product development has slowed since the Broadcom acquisition, and support quality and response times have declined. Some users report the platform feels less actively maintained compared to competitors.
Our Take
We think Symantec PAM may suit organizations already running Broadcom security products that need a PAM solution integrated into their existing stack. For new deployments, we recommend evaluating the current product roadmap and support commitments before committing. The PAM market has moved significantly since Broadcom took over, and several competitors now offer more actively developed platforms with stronger vendor support.
Strengths
- Hardened virtual appliance simplifies deployment
- Integration with Broadcom's broader security stack
- Automated credential rotation and check-in/check-out workflows
- Session recording across Windows, Linux, and Unix
Cautions
- Multiple reviews flag product development has slowed since the Broadcom acquisition
- Users report support quality and response times have declined
CyberArk Privileged Access Manager

CyberArk is the enterprise standard for privileged access management, built for organizations with complex hybrid infrastructure and zero tolerance for credential risk. CyberArk was acquired by Palo Alto Networks in February 2026 for approximately $25 billion, positioning CyberArk’s PAM capabilities as a core identity security pillar within Palo Alto’s broader platform. We found the automated response loop sets CyberArk apart: when suspicious privileged access is detected, the platform terminates the session and rotates credentials without waiting for manual intervention.
CyberArk Privileged Access Manager Key Features
The secure vault anchors the architecture. Continuous scanning detects privileged access attempts across the network, and automated response terminates suspicious sessions and rotates compromised credentials in real time. Full session oversight includes video playback and keystroke capture, giving security teams complete audit records. Deployment options span on-premises, cloud, and SaaS. Identity Threat Detection and Response capabilities feed billions of threat intelligence signals into risk-based access decisions, and centralized reporting ties privileged activity across the full environment into a single view.
What Customers Say
Customers consistently call CyberArk the benchmark for enterprise PAM. Audit readiness is where the reputation holds up strongest, with the vault, session recording, and compliance reporting combination delivering real value at scale. Some reviews note password rotation reliability drops in non-standard configurations, and check-in/check-out can be unreliable in certain setups, requiring manual admin intervention.
Our Take
We think CyberArk fits large enterprises that can dedicate the resources to deploy and maintain it. If audit compliance and hybrid infrastructure are your primary drivers, this platform is built for that environment. Note that the Palo Alto Networks acquisition is recent, so evaluate how the combined platform roadmap affects your deployment plans. If your team is smaller or needs rapid deployment, factor in the operational overhead.
Strengths
- Automated session termination and credential rotation on threat detection
- Continuous network scanning for privileged access attempts
- Full session recording with video playback and keystroke capture
- Flexible deployment across on-premises, cloud, and SaaS
Cautions
- Customers note password rotation reliability drops in non-standard configurations
- Requires significant planning and dedicated technical resources to deploy
Delinea Secret Server

Delinea Secret Server focuses on what happens after users authenticate, giving organizations precise control over what privileged accounts can actually do inside sessions. We think this distinction matters: most PAM platforms focus on getting users in securely, but Secret Server’s fine-grained authorization policies set clear limits on user actions within privileged sessions, reinforcing least privilege beyond just access control.
Delinea Secret Server Key Features
Just-in-time and on-demand privilege provisioning reduce standing access exposure. Custom approval workflows handle delegated access requests without creating bottlenecks. Policy-driven password rotation and complexity enforcement run alongside two-factor authentication for vault access. Session recording uses an industry-leading compression ratio where an hour of video takes less than 5 MB, which matters for organizations with long retention requirements. Integrations span applications, infrastructure, and security platforms.
What Customers Say
Ease of administration stands out in customer feedback. Users say managing access and auditing privileged accounts from a single console simplifies daily operations. Security teams consistently credit the detailed audit visibility as a key operational advantage. Some users report that automated password rotation failures triggered account lockouts in certain configurations.
Our Take
We think Delinea Secret Server fits enterprises that prioritize authorization depth. If your security model requires precise control over what privileged users can do inside sessions, not just who gets access, this platform addresses that directly. If your team needs fast implementation or straightforward credential storage, factor the setup complexity into your evaluation timeline.
Strengths
- Fine-grained policies control what users can do inside privileged sessions
- JIT provisioning and custom approval workflows reduce standing access
- Session recording at less than 5 MB per hour for long retention
- Single-console administration for access management and auditing
Cautions
- Reviews note automated password rotation failures can trigger account lockouts
- Initial setup requires significant effort at enterprise scale
ManageEngine PAM360

ManageEngine PAM360 is a full-lifecycle PAM platform covering credential vaulting, session management, certificate lifecycle management, and SSH key governance. We think the breadth is the differentiator: PAM360 bundles capabilities that typically require separate tools, including SSL/TLS certificate management and SSH key rotation, into one platform. It is part of the broader ManageEngine IT management suite.
ManageEngine PAM360 Key Features
The credential vault supports automated password rotation across servers, databases, network devices, and cloud platforms. Session management covers real-time monitoring, recording, and the ability to terminate sessions from the admin console. The built-in certificate lifecycle management module tracks SSL/TLS certificate expiry and automates renewal workflows, which most PAM platforms do not include natively. SSH key discovery and rotation address a gap that many organizations leave unmanaged. Role-based access controls, approval workflows, and audit reporting round out the compliance story.
What Customers Say
Users praise the all-in-one approach for reducing tool sprawl across PAM, certificate management, and SSH governance. The integration with other ManageEngine products, particularly ServiceDesk Plus, gets positive marks from IT operations teams. Some reviews mention the interface requires time to learn, and customizing reports beyond the defaults involves manual effort.
Our Take
We think ManageEngine PAM360 fits mid-to-large organizations that want PAM, certificate management, and SSH key governance in a single platform. If your team already uses ManageEngine products, the integration adds operational value. Note that pricing varies significantly by tier and administrator count, so request a current quote that matches your deployment scope. For organizations that need only core credential vaulting and session recording, the breadth of PAM360 may be more than you need.
Strengths
- Bundles PAM, certificate lifecycle management, and SSH key governance
- Automated credential rotation across servers, databases, and cloud platforms
- Real-time session monitoring with admin-initiated termination
- Integrates with the broader ManageEngine IT management suite
Cautions
- Reviews mention the interface requires time to learn
- Pricing varies significantly by tier; request a current quote for your scope
Saviynt Cloud PAM

Saviynt Cloud PAM is a cloud-native privileged access management platform that converges PAM with identity governance, application access governance, and identity security posture management in a single platform. We think the convergence story is what sets Saviynt apart: instead of running separate PAM and IGA tools, Saviynt handles both from one control plane with shared policies. Saviynt was named a Leader in the 2025 SPARK Matrix for PAM.
Saviynt Cloud PAM Key Features
Just-in-time and just-enough access provisioning eliminates standing privileges for both human and machine identities. The platform discovers and classifies privileged access across cloud infrastructure, SaaS applications, and on-premises systems. Session monitoring and recording cover privileged activity with full audit trails. Saviynt’s identity governance engine applies access certification, segregation of duties, and risk-based analytics alongside PAM controls, which eliminates the gap between who has access and what they can do. Cloud-native architecture means no appliances or agents to deploy for core PAM functionality.
What Customers Say
Users praise the converged approach for eliminating silos between identity governance and privileged access teams. The cloud-native architecture gets credit for reducing infrastructure overhead. Integration with major cloud platforms and SaaS applications earns positive marks. Some reviews mention the platform’s breadth creates a learning curve during onboarding, and customization of workflows requires dedicated configuration effort.
Our Take
We think Saviynt Cloud PAM fits enterprises that want to unify identity governance and privileged access under one platform rather than integrating separate tools. If your organization already runs Saviynt for IGA, extending into PAM is a natural step. For teams that only need standalone credential vaulting and session recording without governance, a focused PAM tool may be simpler to deploy and manage.
Strengths
- Converges PAM with identity governance and access certification
- Cloud-native architecture with no appliances or agents for core PAM
- JIT and just-enough access for both human and machine identities
- Discovers and classifies privileged access across cloud and on-premises
Cautions
- Reviews mention the platform's breadth creates a learning curve
- Customization of workflows requires dedicated configuration effort
Other Identity And Access Management Services
We researched lots of PAM solutions while we were making this guide. Here are a few other tools worth your consideration:
Scalable PAM with a user-friendly interface, easy integration and cloud-based LDAP, RADIUS and SSH Key management.
Password randomization and encryption, one-time access, and credential rotation to secure shared accounts.
Powerful password management and PEDM that ensures secure privileged access for both internal and remote employees.
What To Look For: PAM Solutions Checklist
- Credential Vaulting And Rotation: Does the platform vault all privileged credentials centrally? Can it automate password rotation on a schedule and on-demand? Does rotation handle service account dependencies without breaking connected systems? Manual credential management is the gap most breaches exploit.
- Session Monitoring And Recording: Does the platform record privileged sessions with full replay capability? Can you search session recordings by command, action, or timeframe? Are recordings tamper-proof for audit evidence? Session visibility is non-negotiable for compliance.
- Just-In-Time Access: Can you eliminate standing privileges with time-bound, approval-based access? Do elevated privileges expire automatically? Can you enforce least privilege at the application or command level? Standing privileges are standing risk.
- Threat Detection And Response: Does the platform detect anomalous behavior during privileged sessions? Can it terminate sessions automatically when risk thresholds are crossed? Does it integrate with your SIEM for correlated alerting? Detection without response is just monitoring.
- Discovery And Onboarding: Can the platform auto-discover privileged accounts across your environment? Does it find orphaned service accounts and unmanaged credentials? How quickly can you bring discovered accounts under management? You cannot protect what you do not know exists.
- Deployment Flexibility: Is this cloud-native, on-premises, or hybrid? Can you deploy in air-gapped environments if regulations demand it? What infrastructure does the platform require? Deployment model affects time to value and operational overhead.
- Compliance Reporting: Does the platform generate audit-ready reports for your regulatory requirements? Can it map access events to specific compliance frameworks? Are compliance exports customizable? Auditors want evidence, not raw logs.
- Integration Depth: Does it integrate with your identity provider, SIEM, ticketing system, and cloud platforms? Are integrations native or do they require custom development? How much effort does initial integration require? Isolated PAM creates gaps in your security posture.
Weight these criteria based on your maturity level. Organizations building their first PAM program should prioritize credential vaulting and session recording. Mature programs need threat detection and just-in-time controls. Regulated industries should lead with compliance reporting and audit evidence.
How We Compared The Best Privileged Access Management (PAM) Solutions
Expert Insights is an independent editorial team that researches, tests, and reviews privileged access management solutions. No vendor can pay to influence our review of their products.
We evaluated 11 PAM platforms across credential vaulting capabilities, session monitoring depth, just-in-time access controls, automated credential rotation, threat detection and response, and deployment flexibility. We assessed admin console usability, integration depth with identity providers and SIEM platforms, and compliance reporting capabilities. Testing covered cloud-native, on-premises, and hybrid deployment models.
Beyond hands-on evaluation, we conducted extensive vendor market mapping and reviewed customer feedback from organizations in financial services, healthcare, government, and enterprise IT. We spoke with security teams to validate where vendor claims diverge from real-world deployment experience. Our editorial and commercial teams operate independently. No vendor can pay to influence our review of their products.
This guide is updated quarterly to reflect product releases and market changes. For full details on our testing methodology, visit our How We Test & Review Products.
The Bottom Line
Your ideal PAM solution depends on your infrastructure complexity, compliance requirements, and team capacity.
If you need the enterprise benchmark for privileged access security, CyberArk Privileged Access Manager delivers active threat response with automatic session termination and credential rotation. Plan for significant implementation effort.
For mid-sized teams that want PAM without a separate infrastructure project, KeeperPAM builds directly on an existing Keeper vault. Session recording, zero-knowledge architecture, and compliance coverage at a practical price point.
If endpoint privilege control is your priority, ThreatLocker Elevation Control removes blanket admin rights and replaces them with application-specific elevation. Ringfencing adds a layer most PAM tools skip entirely.
If your organization wants PAM and identity governance unified, Saviynt Cloud PAM eliminates tool sprawl with just-in-time access and automatic expiration on one platform. ManageEngine PAM360 is the budget-conscious choice for teams building their first PAM program, starting at $7,995 per year.
Read the individual reviews above to understand credential vaulting depth, session monitoring capabilities, deployment requirements, and operational trade-offs that matter for your environment.
 FAQs
FAQs
Privileged Access Management Solutions: Everything You Need To Know
“Privileged access” refers to the elevated access permissions that IT and security admins can assign to user accounts, that give those accounts administrative levels of access to critical systems and applications.
Most organizations organize their systems in tiers, according to the severity of the consequences should the system be breached or misused; the higher the tier, the more damage a breach would cause. Privileged accounts, such as domain admin or local administrator accounts, are granted higher levels of permissions than standard user accounts. These permissions give them administrative levels of access to high-tier systems.
If a cybercriminal were to compromise a privileged account by stealing or cracking its credentials, they could:
- Access critical business systems and applications undetected
- Make changes to the account or to business data
“Standing privileges” are elevated access privileges that are always on. If a user has standing privileges, it means that they always have those privileges assigned to their account, even if they’re not currently using them. A user may not even be aware that they have those privileges.
A common example of standing privilege is the “admin” account that often comes pre-made with a new laptop or desktop, or when you install a new cloud application.
The problem: If an attacker were to compromise a privileged account by stealing or hacking the user’s login credentials, they would be able to use that account to access critical business resources multiple times.
The solution: The best way to mitigate risk associated with standing privileges is by implementing a “just-in-time” approach to elevating access privileges, also known as the “principle of least privilege.”
This principle states that IT, security, and compliance teams should only grant elevated permissions when they’re needed, and for the amount of time they’re needed. Once the user logs out of the system, the elevated permissions and revoked. In other words, every user has just enough access to do their job at all times.
So, if an attacker compromises an account with just-in-time privileges, they’ll only be able to utilize those elevated permissions once— this greatly limits the amount of damage they can do.
Privileged Access Management (PAM) is the process of identifying privileged users and ensuring they have a reasonable level or access, or revoking levels of access that are unnecessary.
This stops cybercriminals from being able to access privileged accounts by greatly reducing the time period during which the credentials are valid.
Privileged access management (PAM) software enables IT and security teams to assign, monitor, and secure privileged access to high-tier business systems and applications. This involves:
- Securely elevating privileges in line with the principle of least privilege
- Eliminating standing privileges
- Monitoring user activity within high-tier systems
To achieve this, PAM tools usually work in one of two ways:
- The PAM solution stores privileged login credentials in a secure vault that is only accessible after identity has been verified through multi-factor authentication. This ensures that only legitimate, authorized users can access privileged credentials. Some PAM solutions give users access to the credential vault; others inject the credentials directly into the user’s login session once they’ve authenticated, so that they never see the credentials. This prevents users from exposing credentials in a phishing attack. In both cases, the PAM solution logs who requested access, when, from where, and for how long.
- The PAM solution offers a system by which users can submit a request for elevated privileges on-demand. The solution then notifies IT or security admins of the request, and they can grant or deny the user access on a case-by-case basis or set up automatic, role-based provisioning.
The best PAM tools also enable admins to monitor a user’s activities during their privileged session. This can help identify malicious activity and can also be used for regulatory compliance and auditing. The level of monitoring varies between solutions; some offer activity logs, while others offer full video recordings and keystroke monitoring.
There are numerous benefits to implementing a PAM solution:
- Control access to your data. By reducing the number of accounts that have elevated privileges, a PAM solution can help you minimize the likelihood of an attacker gaining access to a privileged account using stolen credentials. This, in turn, reduces the likelihood of a data breach, or a malware attack that requires elevated privileges to run, such as an SQL injection.
- Identify compromised accounts. PAM solutions provide greater visibility into account use, thereby making it much easier to spot an attack.
- Reduce repeat attacks. By eliminating standing privileges and rotating login credentials in between privileged sessions, PAM solutions prevent attackers from using the same credentials to access your company’s systems twice, greatly limiting the damage they can do.
- Prove compliance. PAM solutions generate reports explaining which users have elevated access privileges and for which applications. These reports should detail when those privileges are used, and what activities the user performs during a privileged session. These reports can be used to prove compliance with strict data protection regulations such as HIPAA, PCI-DSS, and SOX—all of which require that businesses apply least-privilege access policies to critical accounts containing sensitive data.
Identity and access management (IAM) and privileged access management (or privileged identity management) are similar, but not the same.
IAM is a series of tools and processes (such as multi-factor authentication and single sign-on) that are used to verify and authorize users across an entire organization. This enables IT and security teams to control who can access what, from which locations, when, and how. In IAM, the verification process usually takes place when a user first signs into their user account. A user’s credentials (including alternative authentication factors) are used to verify their identity.
PAM is a subset of IAM that focuses solely on privileged users who need to access more sensitive data. In PAM, verification takes place when a user tries to access a specific resource. And while PAM solutions often include MFA as a means of verifying users before they can be granted elevated privileges, PAM ultimately bases its identity validation on attributes, rather than credentials.
IAM gives authorized users access. PAM gives users just enough access.
- The Top 11 Identity And Access Management Solutions
- The Top 8 Customer Identity And Access Management (CIAM) Solutions
- The Top 7 Identity Threat Detection and Response (ITDR) Solutions
- The Top 5 Credential Management Solutions
- The Top 10 Identity Verification Software
- The Top 10 Fraud Detection and Prevention Solutions
- The Top 9 Solutions To Stop Account Compromise
- The Top 5 Decentralized Identity Solutions
- The Top 7 Know Your Business (KYB) Solutions
- The Top 10 KYC (Know Your Customer) Solutions
- The Top 10 Alternatives To Microsoft Azure Active Directory
- The Top 10 Alternatives To Okta Workforce Identity
- The Top 10 Alternatives To RSA SecurID
- The Top 10 Alternatives To Delinea PAM
 Written By
Written By
Caitlin Harris is the Deputy Head of Content at Expert Insights. As an experienced content writer and editor, Caitlin helps cybersecurity leaders to cut through the noise in the cybersecurity space with expert analysis and insightful recommendations.
Prior to Expert Insights, Caitlin worked at QA Ltd, where she produced award-winning technical training materials, and she has also produced journalistic content over the course of her career.
Caitlin has 8 years of experience in the cybersecurity and technology space, helping technical teams, CISOs, and security professionals find clarity on complex, mission critical topics like security awareness training, backup and recovery, and endpoint protection.
Caitlin also hosts the Expert Insights Podcast and co-writes the weekly newsletter, Decrypted.
 Technical Review
Technical Review
Laura Iannini is a Cybersecurity Analyst at Expert Insights. With deep cybersecurity knowledge and strong research skills, she leads Expert Insights’ product testing team, conducting thorough tests of product features and in-depth industry analysis to ensure that Expert Insights’ product reviews are definitive and insightful.
Laura also carries out wider analysis of vendor landscapes and industry trends to inform Expert Insights’ enterprise cybersecurity buyers’ guides, covering topics such as security awareness training, cloud backup and recovery, email security, and network monitoring. Prior to working at Expert Insights, Laura worked as a Senior Information Security Engineer at Constant Edge, where she tested cybersecurity solutions, carried out product demos, and provided high-quality ongoing technical support.
Laura holds a Bachelor’s degree in Cybersecurity from the University of West Florida.