Best 11 Cyber Threat Intelligence Solutions For Enterprise (2026)
We reviewed 11 cyber threat intelligence platforms on the relevance and freshness of intelligence, how well each integrates with SIEM and SOAR tools, and whether the output drives faster response or just adds to the analyst reading list.
 Technical Review by
Laura Iannini
Technical Review by
Laura Iannini
Quick Summary
Cyber threat intelligence (CTI) solutions deliver timely, actionable intelligence on threat actors, malware campaigns, and emerging attack techniques — enabling security teams to improve detection and accelerate response. Generic threat intelligence provides context; operationalized intelligence drives action, and the gap between them determines the value of a CTI platform. We reviewed 11 platforms and found NordStellar, ESET Threat Intelligence, and Flare to be the strongest on intelligence relevance and SIEM/SOAR integration quality.

Cyber threat intelligence (CTI) solutions are designed to provide businesses like yours with timely, actionable, and relevant intelligence on potential cybersecurity threats, allowing them to take action before an attack occurs.
Automation is a key feature for many of these solutions. While most vendors provide a combination of automation and specialist analysis services, these solutions can actively scan, analyze, and feed back intelligence at a much faster rate than a human analyst can.
But each cyber threat intelligence solution works slightly differently. Some might shine for their advanced automation capabilities, and others might be better suited to organisations that are looking for more of a human-led approach.
Throughout our guide, we’ve included a range of the most dynamic, innovative, and powerful cyber threat intelligence solutions on the market.
Top 11 Cyber Threat Intelligence Solutions Shortlist
- NordStellar – Best for organizations needing consolidated dark web monitoring and attack surface management
- ESET Threat Intelligence – Best for teams needing structured APT intelligence at an accessible price point
- Flare – Best for organizations needing dark web monitoring with active remediation capabilities
- CrowdStrike Adversary Intelligence – Best for organizations already running CrowdStrike products
- Cyware Threat Intelligence Platform – Best for enterprise SOC teams managing multiple threat intelligence feeds
- ManageEngine Log360 – Best for hybrid environments needing unified SIEM, DLP, and compliance reporting
- IBM Security X-Force – Best for enterprises needing managed threat intelligence paired with incident response
- Google Cloud’s Mandiant – Best for enterprises needing expert-backed intelligence with managed detection
- Palo Alto Cortex XSOAR – Best for organizations already running Palo Alto products
- Recorded Future – Best for teams needing broad, multilingual threat intelligence with dark web coverage
- ZeroFox – Best for organizations facing brand impersonation and dark web exposure risks
NordStellar is a threat exposure management platform that combines dark web intelligence, attack surface management, and cybersquatting detection in one console. We were impressed by how the platform consolidates multiple intelligence streams that organisations typically buy as separate tools.
NordStellar Key Features
The alert prioritisation stands out. NordStellar ranks exposures by impact, exploitability, and breach probability, which means your team spends less time triaging and more time remediating. The dark web monitoring covers over 25,000 cybercriminal communities, tracking leaked credentials, data breaches, and brand mentions. Attack surface management maps your external footprint and flags misconfigured assets. The platform integrates with existing SOC/SIEM and incident response workflows.
What Customers Say
Setup is low friction. Customers highlight that you provide your company domain and the platform starts working. The team behind NordStellar is accessible and responsive, which matters for a newer platform. Something to be aware of is that the platform is still maturing, with deeper capabilities being requested over time, and limited long-term customer feedback is available given its relative newness.
Our Take
We were impressed by the consolidated approach here. If your team needs dark web monitoring, attack surface management, and brand protection without managing three separate tools, NordStellar delivers that in a single platform.
Strengths
- Prioritises alerts by breach probability and business impact, reducing triage time
- Monitors over 25,000 cybercriminal communities for credentials and brand mentions
- Low setup overhead with domain-based onboarding
- Integrates with existing SOC/SIEM and incident response workflows
Cautions
- Customers note the platform is still maturing, with deeper capabilities being requested over time
- Limited long-term customer feedback available given the platform's relative newness
ESET Threat Intelligence is a threat intelligence service focused on APT group tracking and curated threat feeds. We think it is a strong fit for security teams that need structured nation-state intelligence without enterprise-scale pricing.
ESET Threat Intelligence Key Features
The standout here is persistent monitoring of APT groups operating out of Russia, China, North Korea, and Iran. The curated feeds provide structured intelligence that goes beyond raw IOCs, giving your team context on adversary behaviour and tactics. Automated threat investigation keeps intelligence flowing without manual triggers. The premium tier includes direct analyst access for hands-on threat discussions. Entry-level pricing starts at $211 per five users per year.
What Customers Say
Customers describe the platform as mature and well thought out, with easy integration into existing environments. Long-term loyalty gets mentioned repeatedly, with some customers citing over a decade of use. Something to be aware of is that the UI feels cluttered and harder to navigate than competitors, and the platform is focused on APT intelligence rather than broader threat exposure management.
Our Take
If your team needs structured APT intelligence at an accessible price point, ESET is well worth considering. Entry-level pricing starts low enough that smaller teams can justify the investment, and the premium tier opens direct analyst access for deeper collaboration.
Strengths
- Tracks APT groups across multiple nation-states with continuous, structured monitoring
- Automated threat investigation keeps intelligence flowing without manual triggers
- Premium tier includes direct analyst access for hands-on threat discussions
- Entry pricing at $211 per five users per year keeps it accessible for smaller teams
Cautions
- Reviews mention the UI feels cluttered and harder to navigate than competitors
- Focused on APT intelligence rather than broader threat exposure management
Flare is a threat intelligence and dark web monitoring platform built for tracking cybercrime exposure across thousands of sources. We think the combination of deep source coverage and autonomous remediation sets it apart from platforms that stop at alerting.
Flare Key Features
The source coverage is strong. Flare monitors cybercrime forums, dark web marketplaces, and over 58,000 Telegram channels while archiving content for investigation even after takedowns. Autonomous remediation moves beyond passive monitoring into active threat response. The enrichment layer adds context to alerts, helping analysts triage faster without switching tools.
What Customers Say
Long-term users praise the alerting system and the actionable guidance that comes with each alert. Support gets consistently high marks, with customers noting the team actively incorporates feedback. Something to be aware of is that the interface has a learning curve, especially for GUI-focused workflows, and documentation lacks practical examples around search query syntax.
Our Take
If your organization needs dark web monitoring that goes beyond passive intelligence into active remediation, Flare fits that need. The archived content capability is particularly useful for investigations where source material disappears quickly.
Strengths
- Archives dark web content for investigation even after takedowns
- Monitors over 58,000 Telegram channels alongside cybercrime forums and marketplaces
- Autonomous remediation moves beyond passive monitoring into active threat response
- Strong customer support with responsive feedback loops
Cautions
- Users report the interface has a learning curve, especially for GUI-focused workflows
- Reviews flag that documentation lacks practical examples around search query syntax
CrowdStrike Adversary Intelligence

Founded in 2011, CrowdStrike is a global provider of cloud-native security solutions and is particularly well known for its endpoint protection platform. CrowdStrike Adversary Intelligence, formerly Falcon X, is a threat intelligence platform that combines dark web monitoring, adversary profiling, and automated threat analysis. What sets CrowdStrike apart is its detailed and contextualised integrated threat intelligence, which provides not only details of an attack but also the wider motivation and expertise of the threat actor behind it, helping admins strengthen their defense. We think Adversary Intelligence slots in naturally for organisations already running CrowdStrike products.
CrowdStrike Adversary Intelligence Key Features
We found the pre-built incident response playbooks to be a practical accelerator for SOC workflows. Rather than building response procedures from scratch, teams can deploy field-tested playbooks and customise them to their environment. The platform tracks 281+ adversaries across open, deep, and dark web layers. The advanced malware sandbox provides AI-powered analysis and classification, and the threat intelligence feeds deliver structured IOCs that map to MITRE ATT&CK. CrowdStrike’s intelligence is popular with Fortune 100 organisations, as well as those in the finance, healthcare, and energy industries.
What Customers Say
Customer feedback here draws from the broader CrowdStrike platform rather than Adversary Intelligence specifically, which makes isolating module-specific strengths harder. The fast, thorough, and accurate intelligence gets positive marks, as does the option for a dedicated intelligence team in the premium tier. Something to be aware of is that full value often requires investment in additional CrowdStrike products, and module-specific assessment is harder given the platform-wide feedback.
Our Take
If your organization already runs CrowdStrike products, Adversary Intelligence slots in naturally and extends your existing investment. The pre-built playbooks and adversary profiling reduce the time to operationalise intelligence. Standalone buyers should weigh the value against the platform dependency.
Strengths
- Pre-built incident response playbooks accelerate SOC workflows without custom development
- Tracks 281+ adversaries across open, deep, and dark web layers
- Advanced malware sandbox with AI-powered analysis and classification
- Integrates tightly with the broader CrowdStrike Falcon platform
Cautions
- Reviews mention full value often requires investment in additional CrowdStrike products
- Customer feedback is platform-wide, making module-specific assessment harder
Cyware Threat Intelligence Platform

Cyware TIP, now branded as Cyware Intel Exchange, automates the threat intelligence lifecycle from ingestion through actioning, with a focus on enterprise SOC teams managing multiple intelligence feeds. We think this fits best in enterprise environments with established SOC operations.
Cyware Threat Intelligence Platform Key Features
The multi-source intelligence ingestion and automatic enrichment pipeline is the core strength here. Cyware TIP pulls in threat data from commercial, open-source, and community feeds, deduplicates and enriches it, and pushes actionable intelligence to connected tools. Bidirectional sharing with trusted communities uses STIX/TAXII standards. The ROI dashboard provides measurable visibility into threat feed effectiveness. Direct integration with SIEM, EDR, MDR, and vulnerability management tools closes the loop between intelligence and action.
What Customers Say
Customers at large enterprises in banking, travel, and services highlight the deduplication and enrichment capabilities as key strengths. Something to be aware of is that bugs and integration issues, particularly with CTIX tooling, are noted, and platform complexity requires onboarding investment for teams new to TIP workflows.
Our Take
We think this fits best in enterprise environments with established SOC operations. If your team manages multiple threat intelligence feeds and needs to automate ingestion, enrichment, and actioning, Cyware TIP delivers that workflow in a single platform.
Strengths
- Automates the full intelligence lifecycle from ingestion through enrichment to actioning
- Bidirectional sharing with trusted communities via STIX/TAXII standards
- ROI dashboard provides measurable visibility into threat feed effectiveness
- Integrates directly with SIEM, EDR, MDR, and vulnerability management tools
Cautions
- Customers note bugs and integration issues, particularly with CTIX tooling
- Platform complexity requires onboarding investment for teams new to TIP workflows
ManageEngine, the IT management division of Zoho Corporation, offers Log360: a unified SIEM, DLP, and CASB solution focused on detecting, prioritizing, investigating, and responding to security threats. The platform deploys machine learning-based anomaly detection, threat intelligence feeds, and rule-based attack detection to identify advanced threats across on-premises, cloud, and hybrid networks.
ManageEngine Log360 Key Features
Log360 collects and analyzes logs from end-user devices, servers, firewalls, and IPS systems, presenting findings through intuitive dashboards and graphical reports for identifying attacks, anomalies, and potential threats. The Vigil IQ engine handles Threat Detection, Investigation, and Response (TDIR) using real-time correlation, User and Entity Behavior Analytics (UEBA), and MITRE ATT&CK framework mapping. SOAR capabilities compile security data into a single console and automate threat resolution workflows. The platform provides real-time auditing of critical Active Directory changes and visibility into cloud infrastructures across AWS, Azure, Salesforce, and Google Cloud Platform, monitoring changes to users, security groups, VPCs, and permissions. For compliance, Log360 offers audit-ready report templates and violation alerts aligned to HIPAA, PCI DSS, GLBA, FISMA, ISO 27001, and SOX.
Our Take
We recommend Log360 for organizations that need comprehensive security analytics and threat intelligence with strong compliance reporting. The combination of SIEM, UEBA, and SOAR in one platform reduces the tool sprawl that comes with managing separate point solutions. The MITRE ATT&CK mapping and Vigil IQ engine give SOC teams a structured approach to threat detection and investigation. If you operate across hybrid environments and need centralized visibility with compliance coverage, Log360 is worth evaluating.
Strengths
- Unified SIEM, DLP, and CASB with machine learning anomaly detection
- Vigil IQ engine maps threats to MITRE ATT&CK framework for structured investigation
- SOAR capabilities automate threat response workflows from a single console
- Audit-ready compliance templates for HIPAA, PCI DSS, SOX, and ISO 27001
Cautions
- Pricing not publicly available; requires contacting ManageEngine for a quote
IBM Security X-Force

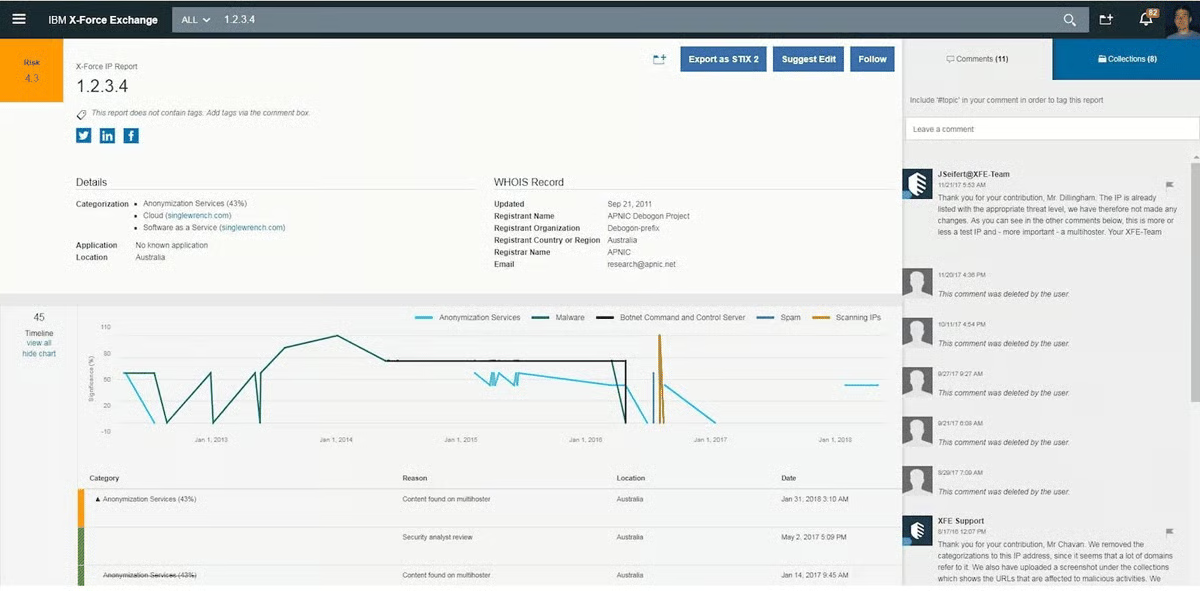
IBM is one of the world’s largest technology providers, making it a strong option for organisations looking for an enterprise-grade, end-to-end threat management solution. IBM Security X-Force is a managed cybersecurity services suite that combines threat intelligence, incident response, adversary simulation, and offensive security capabilities. The platform includes the X-Force Threat Intelligence Index and personalized threat scoring to help organisations prioritize their security investments. We think X-Force delivers the most value for enterprises that need managed threat intelligence paired with incident response capabilities.
IBM Security X-Force Key Features
The depth of the X-Force research team is the primary differentiator here. The X-Force Exchange and Threat Intelligence Insights combine real-time threat feeds, curated research, and structured IOCs. Threat forecasting surfaces emerging vulnerabilities before widespread exploitation. The platform covers the full threat lifecycle from intelligence through response and recovery. Offensive security services, including adversary simulation and cyber range training, round out the capabilities.
What Customers Say
Customers in enterprise environments, particularly banking and semiconductors, highlight the platform’s ability to surface emerging threats with actionable context. The breadth of services across intelligence, response, and offensive security gets positive marks. Something to be aware of is that the managed service model requires sharing organisational data with a third-party provider, and customer feedback is broadly positive but lacks detailed critical insight on specific limitations.
Our Take
If your enterprise needs managed threat intelligence paired with incident response and offensive security capabilities, X-Force delivers depth that few competitors match. The full lifecycle coverage from intelligence through simulation and response is a genuine differentiator at enterprise scale.
Strengths
- Backed by one of the most established commercial security research teams globally
- Covers the full threat lifecycle from intelligence through response and recovery
- Threat forecasting surfaces emerging vulnerabilities before widespread exploitation
- Offensive security services including adversary simulation and cyber range training
Cautions
- Managed service model requires sharing organisational data with a third-party provider
- Reviews note that customer feedback is broadly positive but lacks detailed critical insight on specific limitations
Google Cloud's Mandiant

Founded in 2004, Mandiant is an established cybersecurity company that specializes in threat intelligence and visibility into cyber attacks. Acquired by Google in September 2022, Mandiant Threat Intelligence is now an enterprise-grade intelligence platform backed by one of the most recognised incident response and threat research teams in the industry. The platform manages the collection, analysis, curation, and dissemination of threat intelligence across structured and unstructured sources. Mandiant Threat Intelligence is available via three subscription tiers: Free, Security Operations, and Fusion. We think Mandiant fits enterprises that need expert-backed threat intelligence with managed detection capabilities.
Google Cloud’s Mandiant Key Features
The combination of human expertise and structured threat data is the core value here. Mandiant’s intelligence is curated by over 500 analysts across 30+ countries. Indicator confidence scoring helps prioritize high-fidelity signals over noise. Industry-targeted threat briefings and scheduled hunts tailor intelligence to your sector. The Free subscription enables users to search the platform’s database, while Security Operations and Fusion tiers unlock managed detection, scheduled threat hunts, and full intelligence access.
What Customers Say
Customers in finance, healthcare, and enterprise environments describe Mandiant as a reliable managed detection and response partner. The depth of the research team and the quality of threat briefings get consistently positive marks. Mandiant Threat Intelligence is particularly popular with enterprise-sized organisations, including law enforcement agencies and government entities. Something to be aware of is that full value is realised through managed services rather than self-service, and limited critical customer feedback is available, making long-term pain points harder to assess.
Our Take
If your organization needs expert-backed threat intelligence with managed detection capabilities and you operate at enterprise scale, Mandiant is worth evaluating. The three-tier subscription model lets you start with free access before committing to premium services.
Strengths
- Over 500 analysts across 30+ countries curating threat intelligence
- Indicator confidence scoring helps prioritize high-fidelity signals over noise
- Industry-targeted threat briefings and scheduled hunts tailor intelligence to your sector
- Three subscription tiers allow organisations to scale coverage to budget and maturity
Cautions
- Customers note that full value is realised through managed services, not self-service
- Limited critical customer feedback available, making long-term pain points harder to assess
Palo Alto Cortex XSOAR

Palo Alto Networks is a global provider of enterprise cybersecurity solutions. Cortex XSOAR is a security orchestration, automation, and response platform that includes integrated threat intelligence management capabilities. Threat data is enriched by Palo Alto Networks’ Unit 42 research team, which is a leading resource in threat hunting and analysis and publishes regular threat assessments and reports. Palo Alto Networks offers more than 850 partner integrations via its XSOAR marketplace, making it a strong option for organisations that need to consolidate and act on intelligence from multiple sources. We think Cortex XSOAR integrates naturally for organisations already running Palo Alto products.
Palo Alto Cortex XSOAR Key Features
The threat intelligence management capability is a practical differentiator. Cortex XSOAR TIM aggregates, scores, and distributes threat indicators through automated playbooks. Unit 42 tagging helps analysts quickly separate high-impact threats from routine alerts. The custom feed builder tailors intelligence to your organization’s specific threat profile. Proven performance at scale with environments running 65,000+ endpoint agents. Open API enables integration with SIEM, SOAR, and third-party security tools.
What Customers Say
Customers in manufacturing, telecom, and retail praise the customization and automation capabilities. Teams using XSOAR highlight the efficiency gains from automated playbooks handling repetitive enrichment and triage tasks. Something to be aware of is that there is a steep learning curve with complex configuration, and reporting customization options are limited.
Our Take
If your organization already runs Palo Alto products, Cortex XSOAR integrates naturally and extends your investment. The sensor-driven detection combined with Unit 42 intelligence gives your team both automated and expert-backed threat analysis.
Strengths
- Unit 42 tagging helps analysts quickly separate high-impact threats from routine alerts
- Custom feed builder tailors intelligence to your organization's specific threat profile
- Proven performance at scale with environments running 65,000+ endpoint agents
- Open API enables integration with SIEM, SOAR, and third-party security tools
Cautions
- Reviews mention a steep learning curve with complex configuration
- Users report that reporting customization options are limited
Recorded Future

Founded in 2009, Recorded Future is a global threat intelligence provider that specializes in combining automated, AI-powered data collection with expert human analysis. Acquired by Mastercard in early 2025, Recorded Future uses machine learning and natural language processing to surface emerging threats across open, deep, and dark web sources. Intelligence insights are curated by a combination of Recorded Future’s proprietary Intelligence Graph and expert analysts from the Insikt research team. The platform is built on several modules, including brand, SecOps, threat, vulnerability, third-party, geopolitical, and identity intelligence. We think Recorded Future fits teams that need broad, multilingual threat intelligence with strong dark web coverage.
Recorded Future Key Features
The platform’s ability to retrieve intelligence from deep and obscure parts of the internet is a clear strength. The machine learning engine processes data in 12 languages, which surfaces threats from non-English sources that many competitors miss. The Insikt research team provides exclusive threat actor intelligence beyond public data. Multi-tenant architecture supports MSSP operations with efficient client management. Integration with SIEMs, EDRs, and third-party security tools is straightforward.
What Customers Say
Daily users praise the Insikt research team for delivering exclusive threat actor intelligence. The portal is described as simple to navigate with efficient search and filtering. Something to be aware of is that support quality varies, with some IOC verdict accuracy issues after escalation, and identity module breach alerts show occasional latency.
Our Take
If your team needs broad, multilingual threat intelligence with strong dark web coverage and flexible integration options, Recorded Future is well worth evaluating. The modular approach means you can start with one intelligence stream and expand as your program matures.
Strengths
- Multilingual analysis across 12 languages surfaces threats from global sources
- Insikt research team provides exclusive threat actor intelligence beyond public data
- Multi-tenant architecture supports MSSP operations with efficient client management
- Straightforward integration with SIEMs, EDRs, and third-party security tools
Cautions
- Customers note that support quality varies, with some IOC verdict accuracy issues after escalation
- Users report that identity module breach alerts show occasional latency
ZeroFox

ZeroFox specializes in providing fully managed protection, threat intelligence, and adversary disruption across the public attack surface, including social media and the dark web. The platform combines brand protection, dark web monitoring, and automated takedown services. ZeroFox collects data relating to dark web, brand, fraud, malware, vulnerability, geopolitical, physical, and strategic threats, and is popular with organisations looking for brand protection and takedown capabilities. We think ZeroFox fits organisations facing brand impersonation, phishing, or dark web exposure risks that need managed takedown capabilities.
ZeroFox Key Features
The end-to-end takedown workflow is the standout capability. ZeroFox handles everything from phishing site detection through takedown execution across 80+ partners, disrupting over 1 million threats annually. AI tagging learns alert behaviour over time, reducing false positives. The platform monitors 180+ platforms including social media, forums, and the dark web. Real-time impersonation alerts and a dedicated takedown service are backed by qualified analysts.
What Customers Say
Customers praise the dashboard clarity and the onboarding experience. The support team gets strong marks for recurring check-ins and strategic guidance. Analysts are noted for being highly qualified and providing excellent customer service. Something to be aware of is that takedown timelines can exceed 48 hours depending on registrar cooperation, and initial deployment generates high false positive volume requiring months of tuning.
Our Take
If your organization faces brand impersonation, phishing, or dark web exposure risks and needs managed takedown capabilities, ZeroFox fits that need. The AI-driven alert tuning improves over time, but expect an initial tuning period before false positive volume stabilises.
Strengths
- End-to-end takedown workflow disrupts over 1 million threats annually through 80+ partners
- AI tagging learns alert behaviour over time, reducing false positives
- Monitors 180+ platforms including social media, forums, and the dark web
- Strong onboarding experience with recurring support check-ins
Cautions
- Reviews mention takedown timelines can exceed 48 hours depending on registrar cooperation
- Customers note initial deployment generates high false positive volume requiring months of tuning
Other Security Operations Services
We researched lots of threat intelligence solutions while we were making this guide. Here are a few other tools that are worth your consideration:
Provides detailed insights into fraud, ransomware, account takeover, brand risk, vulnerabilities, physical threats.
Threat analytics, outbreak alerts, research, publications, and presentations to help you identify the threats.
An intelligence hub fed by Fortra's telemetry and insights from the dark web, social media, and law enforcement.
Deep and dark web monitoring, alerts, and intelligence to help you prioritize mitigation efforts and shorten investigations.
Contextualizes threat research and IoCs from a variety of threat feeds to give you an accurate view of threats.
How We Compared The Top Cyber Threat Intelligence Solutions
We assessed each platform across threat detection coverage, intelligence sources, automation capabilities, integration options, reporting quality, managed services availability, pricing models, and real-world customer feedback. Products were evaluated on how effectively they help security teams identify, prioritize, and respond to threats.
What To Look For In Cyber Threat Intelligence Solutions
When selecting a CTI solution, start with the intelligence sources. The platform should cover the sources that matter most to your organization, whether that is dark web forums, nation-state APT tracking, or brand impersonation monitoring. Automation matters; look for platforms that can ingest, enrich, and distribute intelligence without manual intervention. Integration with your existing security stack is critical, particularly SIEM, EDR, and SOAR tools. Consider whether you need a self-service platform or managed intelligence services. Pricing models vary significantly, from entry-level per-user pricing to enterprise-wide managed service contracts. Finally, evaluate the quality and depth of the research team behind the platform, as the difference between raw data feeds and curated, actionable intelligence often comes down to the analysts supporting the product.
The Bottom Line
The CTI market spans from focused dark web monitoring tools to full-lifecycle managed intelligence services. The right choice depends on your organization’s maturity, existing security stack, and the specific threats you face. Organisations already invested in CrowdStrike or Palo Alto platforms will find the most value in their native intelligence modules. Enterprise teams with established SOC operations should evaluate platforms that automate the full intelligence lifecycle. Smaller teams or those new to CTI should consider platforms with accessible pricing and strong onboarding support. For organisations facing brand impersonation or digital risk exposure, dedicated digital risk protection platforms offer capabilities that general-purpose CTI tools do not match.
 FAQs
FAQs
Cyber Threat Intelligence Solutions: Everything You Need To Know (FAQs)
Cyber Threat Intelligence (CTI) describes any data that is gathered and analyzed to answer questions relating to your digital and cyber infrastructure or events. This can be a very broad subject area. Some CTI solutions will focus on your organization, your capabilities, and the active threats that you face. However, CTI also encompass broader trends that may affect entire industries or technologies.
CTI may be used to carry out threat hunting and investigation time into specific types of malware, as well as highlighting suspicious activity. Information can be gathered regarding the malware’s origin, attack method, and Indicators of Compromise (IoCs). This assessment will be based on detection rules and other cybersecurity experts, if the platform offers a Managed service with a skilled Security Operations Center (SOC) team.
This intelligence can be used to identify the malware more quickly in future cases. This, by extension, improves remediation times, keeping your organization more secure.
At the other end of the scale, organizations might use CTI to identify market trends and plan future cybersecurity strategy. In this case, organizations will be looking at the “big picture” – such as new cybersecurity technology to implement – rather than the specific details of an individual threat. The big questions in today’s CTI landscape include AI and its uses in carrying out or defending against attacks, as well as how the metaverse might change the way we work.
Cyber Threat Intelligence can be split into three main intelligence groups, defining the type of intelligence they gather and who it is designed for.
Tactical Intelligence is the most granular and specific form of intelligence that focuses on individual threats.
- Attack behavior
- Indicators of Compromise (IoC)
- Best remediation actions
Operational Intelligence relates to the implementation of policies and effectiveness of security tools overall.
- Configuration policies
- Malware detection rates
- Network dwell time
Strategic Intelligence looks at the big picture, long term trends to plan a multi-year cyber security strategy.
- Emerging threats and vulnerabilities
- Competitor and peer experience
- Cost effectiveness and ROI of cybersecurity tools
Depending on which type of intelligence you need, there will be different solutions on the market, with different preset (and configurable) detection rules. Some platforms may offer intelligence across multiple areas, or package information differently depending on destination. This information has a range of applications and uses, depending on the questions that you ask of it.
Cyber Threat Intelligence is a very broad topic that can have a broad range of applications. Because of this, it can seem overwhelming when trying to identify which features are important for your use-case. In this section, we’ll highlight some of the key features that you should consider when selecting a cyber threat intelligence platform.
- Effective Data Analysis – CTI platforms are able to ingest vast amounts of data from across your digital estate. This information should be properly assessed and analyzed to give accurate and relevant insights. Human users have very little use for vast quantities of raw data but have a lot to gain from processed data and accurate insights.
- Data Collection – Your CTI solution should collect data from across your estate, infrastructure, devices, and wider databases to ensure that its insights are accurate and relevant. The more data your platform has access to, the more reliable your data will be. The exact locations that you gather data from will depend on the type of information that you need, as well as the structure and configuration of your organization. When searching for compromised credentials, for instance, it is important to scan dark web forums and marketplaces.
- Automation – Some platforms deliver automatic responses and remediation. This ensures that any loopholes or errors can be addressed quickly, thereby reducing the time that you are at risk. Effective automation allows you to streamline workflows and improve response times.
- Scalability – Good CTI platforms should be able to manage all the data that you can provide them. As your organization grows, you will increase the amount of data that a CTI platform has access to. Your platform should have capacity for this, ensuring that no data is overlooked and, therefore, no threat is ignored.
- User-Friendly UI – Your platform should provide clear and concise findings and intelligence, allowing you to quickly understand status and events. There should also be ways of generating and sharing specific reports for different parties. Many solutions use clear intelligence graphs and vulnerability reports to share findings with relevant stakeholders.
- Intelligence Quality Ratings – While it would be great if intelligence quality could sit at 100% all the time, this simply isn’t possible. Some CTI platforms will generate an intelligence quality rating, evaluating how strong the intelligence is. High-quality, critical information can then be prioritized over less accurate or less risky data.
When it comes to gathering cyber threat intelligence, you might hear the phrase: “cyber threat intelligence lifecycle”. This is used to outline the ongoing process for collecting, collating, analyzing, and presenting relevant information.
The timeframe for this lifecycle will differ depending on how urgent the information is, and who it is designed to advise. For example, strategic intelligence might only be presented quarterly, while tactical intelligence needs to be presented minute-by-minute to keep your organization safe.
There are six steps that inform how CTI is gathered and presented to relevant parties:
- Requirements
Your organization must decide what type of intelligence you intend to gather. You’ll need to consider who your stakeholders are, and what you would like the outcome of the analysis to be. You might want to explore an attack surface, understand assets, or decide how best to strengthen security implementation.
2. Collection
In this step, data is collected to answer the questions that the requirements demand (step 1). The nature of this data collection depends on the question. This might involve monitoring traffic logs, conducting interviews with experts, or extracting metadata from devices and internal networks. This stage will produce raw data that can be processed in step 3.
3. Processing
Once data has been collected, it will need to be processed and formatted to make it easier to analyze. To do this, data might need to be decrypted or decoupled from personally identifiable information (PII) or other information that is not relevant to the outcomes stated in step 1. This is also the stage where you can evaluate the data for relevance and reliability.
4. Analysis
This stage requires human intervention to make sense of the compiled data, and to identify trends and anomalies. You might perform statistical analysis to understand if threats are increasing or if response times have altered. In essence, this is the stage where you find the answers to the questions asked in step 1.
5. Dissemination
With data that has been processed, you need to be able to share it with relevant stakeholders. Key findings will need to be highlighted with suggestions of how active threats can be remediated. In this stage, you will consider who the intelligence is for, and the level of detail that is required. You might need to reduce or explain jargon and tailor your findings for the relevant audience. This data might be distributed in a variety of ways – from an email to a presentation or hands-on demonstration.
5. Feedback
Once the intelligence has been collected and shared with relevant parties, the target audience needs to consider how they will act upon the findings. Again, the specific details of this action depend on the target audience and their role within the organization. Are they responsible for procuring new cybersecurity solutions, or for tailoring the policies of existing tools?
The remit for CTI can be as broad or as specific as you decide. The level of detail, as well as the data collected, all depends on what questions you set out to ask, and who the answers are being reported to. This is decided in step 1 of the CTI lifecycle. Common areas analyzed as part of the CTI process include:
- Online brand intelligence
- Dark web monitoring
- Domain impersonation
- Social media impersonation and misuse
- Data breach identification
- Vulnerability intelligence and prioritization
There are several companies that offer CTI solutions to gather relevant data and process it to provide relevant intelligence. Many of these solutions will automatically remediate vulnerabilities to ensure your network is as secure as it can be. These solutions can also be used to:
- Validate findings
- Filter out false positives
- Removing anomalous, “noisy” data points
- Provide immediate, automated response
Again, this is a very broad topic with the benefits depending on what you want to investigate with CTI. However, the most common benefits of carrying out cyber threat intelligence include:
Efficient Incident Response
CTI is sometimes described as a cybersecurity “roadmap” – it gives security teams an invaluable insight into how security implementation affects the network and guides them to where more work is needed.
This “roadmap” will ensure that remediation efforts can be quick and effective in light of a cyber-attack. The intelligence can identify where a security breach is likely to have happened, then predict the behavior of an attack, to put your response one step ahead of the attack.
Using CTI helps to identify where a security team should be directing their efforts. As they don’t have to work out which areas need to be focused on, they are able to use their time effectively and efficiently. They won’t spend expensive human time sifting through data that a machine can analyze much quicker. It also ensures that any new security implementation will be specific and targeted. This reduces the number of vulnerabilities within your organization, and helps to ensure you’re investing in the right areas the first time around.
Ultimately, CTI can help to improve efficiency by streamlining your cybersecurity response, thereby proving a good return on investment.
Ensure Compliance
With attacks becoming more sophisticated and complex, regulatory bodies are asking for more significant cybersecurity infrastructure. Regulatory frameworks – such as GDPR, SOX, HIPPA, etc – often mandate what security implementation they expect you to have in place. As part of this, effective CTI might be required to ensure your organization is alert to, and prepared for, attacks.
Insurance companies, too, will require you to have effective tools in place to protect your organization. Not only will CTI identify the effectiveness of your existing security set up, but it can also instruct you on where you can improve. If you follow these recommendations, some insurance providers will reduce your premiums.
Failure to implement CTI, or the recommendations made by CTI, could see your insurance cover invalidated, or result in fines and penalties from regulatory bodies.
For more information about how to qualify for cyber security insurance, you can read our comprehensive article here.
Inform Security Awareness Training (SAT)
The insights provided by CTI are not limited to tailoring policies or suggesting new security tool implementation; CTI can also highlight how your staff can become an important cybersecurity asset. When employees understand the benefits and the limits of a security tool, they are better placed to ensure success.
For example, if an employee understands the significance and the repercussions of a phishing email that has passed through a spam filter, they will be able to act appropriately. They know that a SEG (Secure Email Gateway) is not infallible and are therefore less likely to fall victim to this type of attack. The infromation gained through CTI can inform an SAT solution by highlighting where an organization’s vulnerabilities are. This ensures that users can spend their time completing the most relevant and valuable training.
By gathering information about your network, you can understand the threats you face, and ensure that employees are properly trained to further minimize the risks.
You can read our list of the Top Cybersecurity Awareness Training Solutions here.
Collaborative Knowledge
By sharing details gleaned from your CTI, you can ensure that organizations present a united front against cyberattacks. By improving security infrastructure across the board, you make it harder for attackers to succeed. There is, therefore, less incentive for hackers to pursue cyberattacks as a means of income, which reduces the likelihood of you becoming a target.
Sharing information about IOCs between organizations will allow you to identify these same indicators more readily, should your network be attacked. Beyond this, if your organization is attacked by a specific malware, another organization’s information regarding the remediation of that malware can be invaluable in managing your own remediation efforts. You will have access to information about how a threat responds once inside a network, and the best strategy for its removal.
The core purpose of cyber threat intelligence is to provide you with the knowledge that allows you to preempt future attacks and thwart them before they can strike—to shift your security practices from reactive to proactive. As ThreatQuotient’s Chris Jacob told Expert Insights in our interview with him.
“Threat intelligence allows you to be predictive in your incident prevention and response. The whole idea is that you’re identifying the malware before you’re infected; you know enough about it from your own research and intelligence feeds to be able to recognize it and know how it’s going to move.”
Having access to the accurate intelligence at the right time enables you to predict and prioritize threats, ensuring that you can implement the right protection to safeguard your organization.
 Written By
Written By
Alex is an experienced journalist and content editor. He researches, writes, factchecks and edits articles relating to B2B cyber security and technology solutions, working alongside software experts.
Alex was awarded a First Class MA (Hons) in English and Scottish Literature by the University of Edinburgh.
 Technical Review
Technical Review
Laura Iannini is a Cybersecurity Analyst at Expert Insights. With deep cybersecurity knowledge and strong research skills, she leads Expert Insights’ product testing team, conducting thorough tests of product features and in-depth industry analysis to ensure that Expert Insights’ product reviews are definitive and insightful.
Laura also carries out wider analysis of vendor landscapes and industry trends to inform Expert Insights’ enterprise cybersecurity buyers’ guides, covering topics such as security awareness training, cloud backup and recovery, email security, and network monitoring. Prior to working at Expert Insights, Laura worked as a Senior Information Security Engineer at Constant Edge, where she tested cybersecurity solutions, carried out product demos, and provided high-quality ongoing technical support.
Laura holds a Bachelor’s degree in Cybersecurity from the University of West Florida.