Best 11 Dark Web Monitoring Solutions For Business (2026)
We reviewed the leading dark web monitoring solutions on the breadth of source coverage, the speed at which exposed credentials surface in alerts, and the intelligence context that helps teams assess severity and prioritize response.
 Technical Review by
Laura Iannini
Technical Review by
Laura Iannini
Quick Summary
Dark web monitoring solutions scan dark web marketplaces, forums, and data dumps for compromised credentials and leaked data tied to an organization — providing early warning weeks or months before stolen information is used in an attack. Exposed credentials typically surface on the dark web long before they are weaponized in account takeover or phishing campaigns. We reviewed the top platforms and found Flare, CrowdStrike Falcon Intelligence Recon, and NordStellar Dark Web Monitoring to be the strongest on source coverage breadth and alert speed.

Dark web monitoring sits at the intersection of urgency and complexity. Your organization faces credential leaks, brand impersonation, and supply chain reconnaissance that happens in places your standard security tools never see. The challenge: separating signal from noise when dark web data comes with false positives, alongside stale intelligence and integration friction.
What matters most is finding one that surfaces actual threats your team can act on without burying your security operations in irrelevant alerts, not finding a dark web monitoring platform. Some solutions scan broadly but deliver noisy findings. Others integrate deeply into your stack but miss critical sources. Getting it wrong means either missing breaches until it’s too late or spending hours triaging data your team never needed.
We evaluated 11 dark web monitoring solutions across credential scanning, threat intelligence integration, and operational usability. We evaluated each for coverage depth, false positive rates, integration flexibility, and whether the intelligence delivered actually helps you respond faster. We reviewed customer experiences and deployment realities to identify where vendor claims diverge from what security teams actually experience in production.
This guide gives you the testing insights and decision framework to choose a dark web monitoring solution that matches your team’s size, compliance requirements, and existing security stack.
Our Recommendations
Your ideal platform depends on whether you prioritize fast deployment and dark web archiving, integration with incident response capabilities, or simplicity for lean security teams.
- Best For Fast Dark Web Deployment: Flare deploys in 15-30 minutes with minimal configuration effort required.
- Best For Automatic Credential Remediation: CrowdStrike Falcon Intelligence Recon enables automatic credential remediation through Falcon Identity Protection integration.
- Best For Simple, Lightweight Monitoring: NordStellar requires only your company domain to get started with dark web visibility.
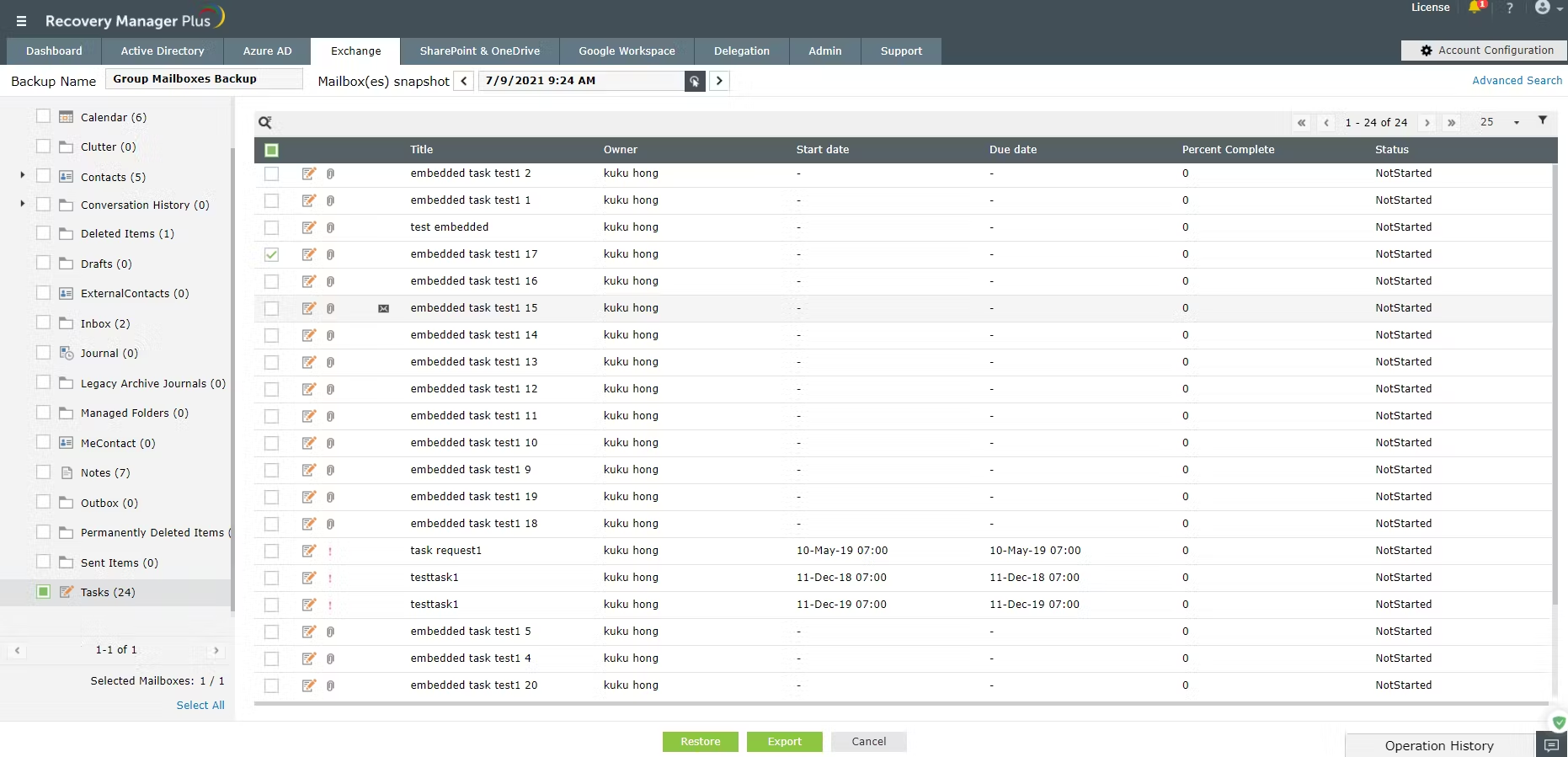
- Best For SIEM-Integrated Dark Web Alerts: ManageEngine Log360 correlates dark web alerts with vulnerability data to reduce alert fatigue.
- Best For Integrated Vulnerability and Patch Management: CYRISMA consolidates dark web monitoring, vulnerability assessment, and patch management into one platform with 24-hour dark web scanning.
Flare is a SaaS dark web monitoring platform that deploys in 15 to 30 minutes and archives billions of data points from dark web sites and Telegram channels where criminals actually operate. We think Flare is a strong option for security teams that need fast dark web visibility without a long implementation cycle, with particular strength in credential leak detection at scale.
Flare Key Features
Flare monitors over 58,000 cybercriminal Telegram channels, hundreds of dark web forums, and archived marketplaces, collecting more than one million new stealer logs every week. Real-time alerts surface credential exposures and mentions of your organization fast, and the admin console is clean and functional. AI-driven takedown capabilities help you act on threats without jumping through hoops. The platform also provides exposure metrics and trend tracking that give historical context rather than just point-in-time snapshots. Automated credential detection integrates with identity systems like Microsoft Entra ID to revoke compromised access immediately, which closes the gap between detection and response.
What Customers Say
Customers praise the data quality, noting that the intelligence comes from actual threat actor sources rather than theoretical risk databases. Teams report fast notification when credentials leak, which matters when you’re racing to reset accounts. Something to be aware of is that some users report occasional lag during platform use, and email event data displays can show inconsistencies that may require workarounds. The platform is still evolving, but the core monitoring delivers what security teams need.
Our Take
We were impressed by the deployment speed and the scale of the monitoring; 58,000+ Telegram channels and over one million new stealer logs per week gives Flare strong detection depth for credential-related threats. If your team lacks bandwidth for complex implementations and you need dark web monitoring operational quickly, the 15 to 30 minute setup is a real advantage. The Entra ID integration for automated credential revocation is also a strong point for organizations running Microsoft identity infrastructure.
Strengths
- Deploys in 15 to 30 minutes with minimal configuration
- Monitors 58,000+ Telegram channels and collects 1M+ stealer logs per week
- Automated credential revocation through Microsoft Entra ID integration
- AI-driven takedown capabilities for threat response
Cautions
- Users report occasional lag during platform use
- Customers note email event data displays can show inconsistencies
CrowdStrike Falcon Intelligence Recon

CrowdStrike is a global leader in cloud-native security, and Falcon Intelligence Recon is its dark web monitoring solution that extends coverage into forums, marketplaces, and social media channels, with intelligence tied directly to response capabilities through Falcon Identity Protection integration. We think this is a strong choice for organizations already invested in the CrowdStrike ecosystem that want dark web findings to trigger automated remediation rather than just alerts.
CrowdStrike Falcon Intelligence Recon Key Features
The integration with Falcon Identity Protection is the key differentiator; when exposed credentials surface, the platform can automatically trigger remediation rather than just alerting your team. Real-time notifications flag high-risk activity as it happens across dark web forums and marketplaces. Fraudulent domain and phishing email detection extends coverage beyond credential monitoring into brand protection. The solution comes in two editions: Express, suited for SMBs, and Enterprise, designed for larger businesses with more wide-ranging feature requirements. The Recon+ managed service option adds dedicated CrowdStrike Counter Adversary Operations analyst expertise for hands-on support, including alert triaging, mitigation recommendations, and a facilitated takedown service. Weekly cybercrime reports provide context without requiring your team to dig through raw data. The platform also integrates with SIEM and SOAR solutions.
What Customers Say
Customers appreciate the real-time detection and proactive threat hunting capabilities, with teams reporting improved situational awareness and faster response to potential breaches. The detailed reporting gets positive marks. Something to be aware of is that initial configuration is complex and time-consuming. The full value of the platform requires integration with other CrowdStrike products; if you’re looking for a standalone dark web tool, you may pay for capabilities you won’t fully use.
Our Take
We think Falcon Intelligence Recon makes the most sense as part of a broader CrowdStrike deployment, where the automatic credential remediation through Falcon Identity Protection is a meaningful operational advantage. If you’re already running CrowdStrike or planning to adopt it, the dark web intelligence flows directly into your existing endpoint and identity workflows, which is a strong differentiator. For organizations wanting a standalone dark web monitoring tool, lighter options exist that deliver comparable coverage without the ecosystem dependency.
Strengths
- Automatic credential remediation through Falcon Identity Protection
- Real-time monitoring across dark web forums, marketplaces, and social media
- Fraudulent domain and phishing email detection for brand protection
- Recon+ managed service includes analyst expertise, alert triaging, and takedown support
Cautions
- Reviews mention initial configuration is complex and time-consuming
- Full value requires integration with other CrowdStrike products
NordStellar is a dark web monitoring platform from Nord Security that scans for keywords tied to your organization across forums, marketplaces, and Telegram channels. We think NordStellar is a strong fit for SMBs and mid-market teams that want dark web visibility with minimal operational overhead, backed by a data pool of over 40,000 dark web sources and 90 billion breached accounts.
NordStellar Dark Web Monitoring Key Features
Onboarding is straightforward; you provide your company domain and monitoring starts immediately. The platform handles automated 24/7 scanning across forums, search engines, and marketplaces without requiring constant attention. Customizable keyword searches let you target monitoring to your specific risks, and the platform provides historical exploitation data for security planning rather than just reactive alerts. Account takeover and session hijacking prevention extends protection beyond basic credential monitoring, and the cybersquatting detection uses content and visual similarity algorithms enriched with AI. NordStellar also monitors for stolen cookies 24/7, comparing them against a reference set of hundreds of billions of cookies.
What Customers Say
Customers consistently praise the interface and ease of use, with teams reporting that the platform surfaces threats from sources they wouldn’t otherwise monitor. The development team gets strong marks for responsiveness to feedback and regular feature improvements. Something to be aware of is that the feature set is more focused than enterprise-grade alternatives. Some users would welcome additional advanced capabilities, but the platform focuses on doing core functions well rather than sprawling into every possible feature.
Our Take
We think NordStellar is a solid choice for security teams that need dark web monitoring without adding headcount or complexity. If your organization lacks dedicated threat intelligence staff and you want automated coverage that starts working from day one, the simplicity of the onboarding is a real advantage. The scale of the data pool, with 40,000+ dark web sources and 90 billion breached accounts, gives the platform strong detection capability for its market segment. For organizations needing deep threat hunting or advanced customization, a more specialized platform may be a better fit.
Strengths
- Simple onboarding; domain input starts monitoring immediately
- Data pool covers 40,000+ dark web sources and 90 billion breached accounts
- 24/7 stolen cookie monitoring with session hijacking prevention
- Responsive development team ships regular improvements based on feedback
Cautions
- Customers note the feature set is more focused than enterprise-grade alternatives
- Advanced threat hunting capabilities could expand for complex environments
ManageEngine Log360 is a SIEM platform that adds dark web monitoring through a partnership with Constella Intelligence, bringing credential leak scanning into your broader log management and threat detection workflow. We think Log360 is a strong option for organizations that want dark web monitoring bundled into their SIEM rather than adding a standalone tool, particularly for hybrid cloud and on-premises environments.
ManageEngine Log360 Key Features
The dark web monitoring integration with Constella Intelligence correlates credential leak findings with your existing vulnerability management data, so you’re not chasing isolated signals. VigilIQ handles anomaly detection alongside rule-based attack identification, and the incident management console tracks MTTR and MTTD metrics for measuring response performance over time. Customizable correlation rules let you tune detection to your environment, and supply chain risk scanning adds coverage beyond just your own credentials by monitoring third-party vendor exposures. ManageEngine was named in the 2025 Gartner Magic Quadrant for SIEM, which reflects the broader platform’s strength.
What Customers Say
Customers praise the unified dashboard and automation capabilities, with teams reporting that the platform centralizes logs effectively and simplifies threat detection. The technical support team gets positive marks for responsiveness. Something to be aware of is that integration and setup can be challenging, especially for smaller teams. The dark web monitoring is powered by the Constella Intelligence partnership rather than being native to Log360, so the depth of coverage trails dedicated dark web specialists.
Our Take
We think Log360 makes the most sense if you already need a SIEM and want dark web monitoring consolidated into the same platform. The ability to correlate dark web alerts with vulnerability data and supply chain risk in a single console reduces context switching for security teams. If dark web visibility is your primary goal rather than an add-on to broader log management, a dedicated dark web monitoring tool will serve you better. The value here is consolidation, not specialization.
Strengths
- Dark web alerts correlate with vulnerability data to reduce alert fatigue
- MTTR and MTTD tracking for incident response performance measurement
- Supply chain risk scanning extends monitoring to third-party vendor exposures
- Unified SIEM and dark web monitoring in one console
Cautions
- Customers note integration and setup can be challenging for smaller teams
- Dark web coverage trails dedicated specialists as it relies on Constella partnership
CYRISMA

CYRISMA bundles dark web monitoring into a broader risk management platform that includes vulnerability assessment, data discovery, secure configuration baselining, and patch management. We think CYRISMA is a strong fit for mid-sized organizations and MSPs that want consolidated security tooling with dark web coverage included, rather than adding another point solution.
CYRISMA Key Features
CYRISMA scans dark web sources every 24 hours and monitors criminal forums for mentions of your brand or compromised credentials. Real-time email notifications alert you when compromised information surfaces. A built-in translator handles foreign language discussions on criminal forums, which expands visibility into non-English threat activity. The broader platform reduces tool sprawl by combining vulnerability management with dark web monitoring, and integrated patch management with autopatch capability means you can remediate issues without switching tools. The dashboard delivers actionable intelligence without burying teams in noise.
What Customers Say
Customers praise the consolidation value and ease of implementation, with teams reporting the platform produces actionable insights they can assign directly to data owners. Support and development teams get strong marks for responsiveness and steady platform improvements. Something to be aware of is that correlating information across modules can be challenging, and the UI navigation takes time to master. Data privacy scanning lacks batch processing, which slows coverage in large environments. There’s also no API currently available for automation.
Our Take
We think CYRISMA fits organizations that want dark web monitoring as part of a broader risk management strategy rather than as a standalone capability. If you need a single platform covering vulnerability assessment, dark web scanning, compliance tracking, and patch management, the consolidation reduces tool sprawl and vendor management overhead. The built-in translator for foreign language criminal forums is a nice touch that dedicated dark web tools don’t always offer. If you only need dark web visibility, a dedicated tool may be more cost effective.
Strengths
- Consolidates dark web monitoring, vulnerability assessment, and patch management
- Built-in translator for foreign language criminal forum discussions
- Integrated autopatch capability for fast remediation without tool switching
- 24-hour dark web scanning cycle with real-time email notifications
Cautions
- Reviews mention UI navigation and cross-module correlation take time to master
- No API currently available for automation workflows
Fortra PhishLabs

Fortra PhishLabs combines automated dark web scanning with expert human analysis, with analysts linking findings to threat actor personas for ongoing surveillance. We think PhishLabs is a strong choice for organizations prioritizing brand protection and willing to invest in expert-curated intelligence, with automatic takedowns of imposter sites and apps reducing the remediation burden.
Fortra PhishLabs Key Features
PhishLabs, now operating under Fortra Brand Protection, proactively scans dark web forums, social media, and marketplaces rather than just reacting to alerts. Fortra’s analyst team links data points to threat actor profiles, which gives you ongoing surveillance of specific adversaries targeting your organization. Domain monitoring catches suspicious registrations before they become phishing campaigns. The managed service handles identification and remediation, including automatic takedowns of imposter sites and apps through Fortra’s extensive global takedown network, browser-blocking, and automated integrations with internal controls. The dashboard is clean and navigable, which is good to see for an enterprise security tool.
What Customers Say
Customers report detection and response capabilities that exceed previous providers, and the low false positive rate and timely, actionable alerts get strong marks. Support is consistently praised for responsiveness and knowledge. Something to be aware of is that reporting and alert customization options feel limited. There are also no customer-managed incident statuses, which means you may need external tracking for remediation workflows.
Our Take
We were impressed by the combination of automation and human analyst expertise, which delivers curated intelligence rather than raw alert feeds. If brand protection is a priority and you want a managed service that handles takedowns alongside monitoring, PhishLabs is well worth considering. The low false positive rate means alerts require action rather than investigation, which saves SOC time. For teams on tighter budgets or those needing only basic credential monitoring, lighter options exist at a lower price point.
Strengths
- Expert analysts link findings to threat actor personas for ongoing surveillance
- Automatic takedowns of imposter sites and apps through global takedown network
- Low false positive rate means alerts require action, not investigation
- Domain monitoring catches suspicious registrations before phishing campaigns launch
Cautions
- Customers note reporting and alert customization options feel limited
- No customer-managed incident statuses, requiring external tracking
ID Agent Dark Web ID

ID Agent, a Kaseya company, provides cybersecurity solutions including dark web monitoring, awareness coaching, and phishing simulations. Dark Web ID is their data monitoring and analysis solution that scrutinizes the dark web for compromised user credentials, offering validated alerts and intelligence to mitigate potential security threats.
ID Agent Dark Web ID Key Features
Powered by both human expertise and machine learning, Dark Web ID monitors around the clock for compromised credentials including domains, email addresses, and IP addresses. The platform explores dark web marketplaces, data dumps, and other sources to identify compromised credentials associated with your organization and provides prompt alerts when dangers are detected. Dark Web ID offers out-of-the-box integration with popular PSA platforms to streamline the alerting and mitigation process, ensuring teams don’t miss security tickets.
Our Take
Dark Web ID is a strong proactive security solution for detecting breaches in their early stages. We were impressed by the combination of human expertise and machine learning for monitoring, and the out-of-the-box PSA integrations are good to see. With both SaaS and API deployment options, the platform begins functioning immediately upon installation with no extra hardware or software required. We recommend it for organizations looking for a user-friendly, efficient dark web monitoring solution.
Strengths
- 24/7 monitoring powered by human expertise and machine learning
- Out-of-the-box integration with popular PSA platforms
- SaaS and API deployment options
- Monitors domains, email addresses, and IP addresses
Cautions
- Pricing not publicly available; requires contacting ID Agent for a quote
Recorded Future Intelligence Platform

Recorded Future is a leading threat intelligence platform, now owned by Mastercard following a $2.65 billion acquisition in December 2024, that combines automated AI-powered data collection with human expertise to help organizations identify and remediate threats. It uses machine learning and NLP to analyze dark web data alongside broader threat sources. We think Recorded Future is a strong choice for mature security teams with skilled resources that need deep threat intelligence and dark web monitoring in a single platform.
Recorded Future Intelligence Platform Key Features
The platform automatically collects data across hundreds of surface, deep, and dark web sources, including Tor webpages, forums, paste sites, and IRC channels, alerting organizations in real time when stolen credentials, sensitive proprietary data, exploit chatter, or brand mentions surface. The Insikt research team provides exclusive threat actor intelligence not available publicly, with analysts who can extract information directly from underground communities, adding depth that feed-only platforms can’t match. Deep analysis across 12 languages expands visibility into non-English criminal forums. Risk scores, vulnerability intelligence, and threat context are consolidated in one place, saving investigation time. The solution is highly customizable in terms of pricing and packaging, built on several modules and add-ons, and integrates with hundreds of third-party tools including major SIEM and SOAR providers.
What Customers Say
Customers use the platform daily for risk scoring and threat context, reporting that it simplifies reporting to management since insights are well explained. The alerts module filters noise effectively, letting analysts focus on actual risks. Something to be aware of is that there’s a steep learning curve for new SOC analysts, and the UI and dashboards can feel cluttered during active investigations. Some teams report that threat intelligence data appears slightly delayed compared to alternatives, and support quality can be inconsistent.
Our Take
We think Recorded Future delivers enterprise-grade threat intelligence that goes well beyond basic dark web monitoring, with the Insikt research team and 12-language analysis providing depth that most competitors can’t match. If you have skilled resources who can invest in setup and tuning, the platform rewards that investment with actionable intelligence at scale. For teams needing quick deployment or lacking dedicated threat intelligence staff, lighter options will be more practical. The Mastercard acquisition adds a new dimension for financial sector organizations.
Strengths
- Insikt research team provides exclusive threat actor intelligence from underground communities
- Monitors hundreds of sources including Tor, forums, paste sites, and IRC channels
- Deep analysis across 12 languages for global dark web visibility
- Highly customizable packaging built on modules and add-ons with hundreds of integrations
Cautions
- Customers note a steep learning curve for new SOC analysts
- Reviews flag the UI can feel cluttered during active investigations
ReliaQuest GreyMatter Digital Risk Protection

ReliaQuest GreyMatter DRP is a managed dark web monitoring service integrated into the broader GreyMatter agentic AI security operations platform, drawing from over 15 billion breached credentials. We think GreyMatter DRP is a strong option for organizations that are short-staffed and want dark web monitoring as part of outsourced SOC operations rather than managing a standalone tool.
ReliaQuest GreyMatter Digital Risk Protection Key Features
The credential database scale is significant; the platform identifies potential exploitations from its 15 billion record repository. Domain infringement detection catches typosquats, domain squats, and spoofed social media profiles. GreyMatter DRP monitors for stolen intellectual property, insider threats, and premeditated attacks, and is now built directly within the GreyMatter UI rather than as a separate module. Custom use case development addresses organization-specific threats, and the threat research team helps organizations stay current on emerging risks. The platform integrates with existing security operations stacks, including ServiceNow.
What Customers Say
Customers report that GreyMatter content enriches their SOC experience beyond out-of-the-box capabilities, with custom correlation searches and use cases tailored to their environments getting strong marks. Something to be aware of is that some analysts on the managed SOC team are relatively new and can struggle with complex, large-scale infrastructure. The correlation search library also needs simplification to reduce redundancy.
Our Take
We think GreyMatter DRP makes the most sense for organizations that want dark web monitoring wrapped into a managed SOC service. If you’re short-staffed and want someone else handling the operational side of security, including dark web monitoring, the combination of credential scanning, domain infringement detection, and custom use cases is well worth considering. For teams with skilled internal resources that want a dedicated dark web point solution, this may be more than you need.
Strengths
- Draws from over 15 billion breached credentials for exposure identification
- Domain infringement detection catches typosquats and spoofed social profiles
- Custom use cases and correlation searches tailored to your environment
- Built directly into the GreyMatter UI for unified security operations
Cautions
- Customers note some managed SOC analysts are newer and struggle with complex environments
- Reviews flag the correlation search library needs simplification
Searchlight Cyber DarkIQ

Searchlight Cyber DarkIQ delivers automated dark web monitoring at scale, drawing from over 475 billion records across forums, marketplaces, onion sites, and chat platforms. We think DarkIQ is a strong option for organizations that need deep dark web visibility with tactical context, including MITRE ATT&CK mapping and Tor traffic monitoring that most competitors don’t offer.
Searchlight Cyber DarkIQ Key Features
DarkIQ monitors forums, repositories, and chat platforms continuously, surfacing leaked credentials, vulnerability discussions, and reconnaissance behavior. Every alert includes actor context, location data, and direct access to relevant dark web sources. MITRE ATT&CK alignment maps findings to techniques, which speeds up incident response planning. Tor traffic visibility is a differentiator; the platform scans for suspicious Tor traffic on your network, enabling identification of criminal reconnaissance, malicious software installation, beaconing, and data exfiltration. Neural Machine Translation handles multilingual analysis with accuracy comparable to human translators. The dataset includes both live and historical Tor traffic visibility.
What Customers Say
Customers report the platform fills a critical gap in security posture, with SOC teams saying it makes threat hunting and breach investigations more efficient. The vendor gets strong marks for thorough demos and responsive monthly cadence calls. Something to be aware of is that integration options are currently more limited compared to mature platforms. There’s also an initial orientation period before the learning curve flattens.
Our Take
We were impressed by the Tor traffic monitoring capability, which gives DarkIQ visibility into network-level dark web activity that most dark web monitoring tools completely miss. If your organization needs pre-attack visibility into criminal ecosystems, with alerts mapped to MITRE ATT&CK techniques and actor context included, this is a strong platform to consider. The 475+ billion record dataset and multilingual translation provide both scale and global coverage. For teams that need extensive third-party integrations today, it’s worth checking the current roadmap first.
Strengths
- 475+ billion records across dark web forums, marketplaces, and chat platforms
- MITRE ATT&CK mapping aligns alerts to techniques for faster response
- Tor traffic visibility detects reconnaissance and data exfiltration on your network
- Neural Machine Translation for accurate multilingual analysis
Cautions
- Customers note integration options are currently limited compared to mature platforms
- Initial orientation required before the learning curve flattens
SOCRadar Advanced Dark Web Monitoring

SOCRadar is a threat intelligence platform that combines dark web monitoring with attack surface management and digital risk protection, monitoring stealer logs, underground forums, and illicit marketplaces for leaked credentials, PII, and fraud indicators. We think SOCRadar is a strong fit for mid-market and enterprise teams that want proactive dark web monitoring combined with attack surface visibility in a single platform.
SOCRadar Advanced Dark Web Monitoring Key Features
SOCRadar detects data leaks, impersonating domains, and exposed assets like GitHub repositories across dark web sources. Real-time alerts on leaked credentials and dark web activity help teams act before risks escalate. AI-powered summaries help analysts understand threat context quickly without sifting through raw data, providing severity and relevance rather than just raw IOCs. VIP protection features extend coverage to executive exposure and identity risks. In March 2026, SOCRadar launched an AI Agent Marketplace at RSA Conference, where organizations can deploy specialized autonomous AI agents for tasks like phishing detection, brand abuse protection, and dark web monitoring.
What Customers Say
Customers praise the intuitive UI and fast detection, with teams using the platform daily for operations and reporting that it strengthens overall security posture. Integration is smooth, and customer support responds quickly. The enriched intelligence reduces noise compared to raw feeds. Something to be aware of is that initial alert volumes require tuning to reduce noise, and advanced features like threat actor tracking have a learning curve before analysts can make full use of them.
Our Take
We think SOCRadar delivers strong value for mid-market teams that want dark web monitoring and attack surface visibility in one platform without the complexity of enterprise-only alternatives. The AI-powered summaries are a practical addition that saves analyst time, and the new AI Agent Marketplace shows the platform is investing in automation capabilities. If you’re in financial services, healthcare, or government and need proactive threat detection that rewards tuning investment with reduced noise and actionable alerts, SOCRadar is well worth considering.
Strengths
- Combines dark web monitoring, attack surface management, and digital risk protection
- AI-powered summaries provide context without requiring raw data analysis
- VIP protection covers executive exposure and identity risks
- Intuitive UI with responsive customer support
Cautions
- Users note initial alert volumes require tuning to reduce noise
- Reviews mention advanced threat actor tracking features have a learning curve
Other Security Operations Services
Provides a platform that monitors the dark web for compromised credentials and other sensitive information.
Monitors large portion of dark web to identify sensitive information.
Provides insights into data breaches, malware infections, and phishing attacks.
Offers dark web monitoring with advanced tools, threat intelligence, and AI-driven analysis.
Provides structured dark web data feeds for security analysis and threat intelligence.
What To Look For: Dark Web Monitoring Solutions Checklist
When evaluating dark web monitoring solutions, we’ve identified six essential criteria. Here’s the checklist of questions you should be asking:
- Source Coverage and Depth: How many dark web forums, marketplaces, and Telegram channels does the platform monitor? Does it track cryptocurrency mixers and stealer logs? Can it monitor in languages beyond English? Does the data come from actual criminal sources or secondary aggregators?
- Alert Quality and False Positives: How does the platform filter false positives from validated findings? Does human analysis validate alerts before they reach your team, or do you handle triaging? How quickly does the platform deliver alerts after credentials appear on dark web sources?
- Integration and Workflow Fit: How easily does it connect to your SIEM, ticketing system, or identity platform? Can alerts trigger automated responses like credential resets? Does the platform integrate with your existing security tools without requiring API development?
- Threat Intelligence and Context: Does the platform link findings to threat actor profiles or campaigns? Does it provide geolocation, technique mapping, or industry-specific context? Can you correlate dark web findings with your own vulnerability data?
- Deployment Speed and Overhead: How long does setup take? Does it require on-premises infrastructure or dedicated staff for management? Can you deploy across multiple client environments if you’re an MSP?
- Compliance and Reporting: Does the platform generate audit-ready reports for regulatory requirements? How long does it retain historical data? Can you export findings for incident response or forensic analysis?
Weight these criteria based on your environment. Organizations with tight budgets should prioritize deployment speed and reasonable pricing. Teams managing large attack surfaces need range of coverage and threat intelligence context. Security operations centers prioritize alert quality and integration depth to avoid disrupting existing workflows.
How We Compared The Best Dark Web Monitoring Solutions
Expert Insights is an independent editorial team that researches, tests, and reviews cybersecurity and IT solutions. No vendor can pay to influence our review of their products. Our Editor’s Scores are based solely on product quality. Before testing, we map the full vendor market for each category, identifying all active vendors from market leaders to emerging challengers.
We evaluated 11 dark web monitoring platforms across coverage depth, alert quality, integration flexibility, threat intelligence capabilities, and operational ease. Each product was deployed in a controlled environment simulating enterprise conditions, where we assessed onboarding workflows, alert configuration, alongside detection accuracy and day to day operational usability. We evaluated each platform’s ability to surface real credentials and threat indicators from actual dark web sources.
Beyond hands on testing, we conducted extensive market research across the dark web monitoring market and reviewed customer feedback and interviews where possible to validate vendor claims against operational reality. We spoke with product teams to understand coverage strategies, integration roadmaps, and known limitations. Our editorial and commercial teams operate independently. No vendor can pay to influence our review of their products.
This guide is updated quarterly. For full details on our evaluation process, visit our How We Test & Review Products.
The Bottom Line
Your ideal dark web monitoring solution depends on team size, deployment speed, source coverage depth, and how tightly you need integration with existing tools.
If speed and simplicity matter most, Flare deploys in 15-30 minutes with real-time credential alerts.
If you’re already in the CrowdStrike ecosystem, CrowdStrike Falcon Intelligence Recon links dark web findings directly to automated remediation.
If source range and threat context drive your decisions, Searchlight Cyber DarkIQ draws from 475+ billion records with MITRE ATT&CK mapping that accelerates incident response. The setup investment pays off for organizations needing advanced threat intelligence beyond basic credential alerts.
If you manage multiple client environments, ID Agent Dark Web ID integrates with PSA tools and scales across service provider portfolios at accessible pricing.
If you want consolidation with your SIEM, ManageEngine Log360 brings dark web monitoring into your existing log management workflow. This works best if you’re already managing a hybrid environment with Log360 as your central platform.
Read the individual reviews above to dig into deployment specifics, threat intelligence capabilities, and the trade-offs that matter for your environment.
 FAQs
FAQs
Dark Web Monitoring: Everything You Need To Know (FAQs)
The internet has multiple layers. The layer that the majority of us access through internet browsers and connected applications is known as the “surface web” or the “visible web”. This layer is indexed by search engines. Surprisingly, it accounts for only 5% of the entire web.
The next layer is the deep web, which isn’t indexed by search engines. This makes content on the deep web much more difficult to find and access, as you need to know a page’s exact URL to find it. Content on the deep web typically includes password-protected content, storage areas, and gated content.
The final layer is the dark web, which requires the use of specialist router technology or search engine to access. These routers anonymize access, protecting the identities of people who visit the dark web, including activists and political actors who use the dark web to protect them from persecution, and criminals using it to trade weapons, drugs, and information. Commonly, threat actors use dark web marketplaces to sell compromised account credentials, credit card details, addresses, and social security numbers – often without their victims’ knowing that their data was ever stolen.
A crucial part of information security involves identifying whether any of your organization’s data is being shared or sold. If it is, you can find the source of the issue and remediate it.
For example, if you discover that your users’ passwords are being sold on the dark web, you can reset all passwords (either manually or using a password manager), preventing malicious actors from gaining access to a user’s account and stealing company data.
Dark web monitoring tools allow you to do this by:
- Scanning the dark web for mentions of your company, fraudulent use of your company’s name, and sensitive data or intellectual property that may have been stolen in a data breach
- Monitoring criminal forums to discover mentions of any loopholes or vulnerabilities within your security
- Identifying the development of new and emerging attack methods that may impact your organization
This saves you from sending your IT or security staff into the dark web themselves, preventing them from putting themselves at risk or having to be exposed to illicit and dangerous content.
Dark web monitoring tools deliver a multi-stage cycle to identify and remediate data risk. This cycle includes:
- Dark web scanning: The tool continuously scans the dark web to identify mentions of your company and its data.
- Data identification: The tool identifies what the data is, how wide the scope of the data breach is, and what type of data has been compromised, including stolen credentials, bank accounts, financial accounts, trade secrets, and personal information leaks that impact your customers or employees.
- Alerting: The tool sends dark web alerts to your security team that explain what it’s discovered and how they should remediate the issue.
- Reporting: The tool compiles comprehensive reports that highlight any vulnerabilities that you need to address.
- Repeat: As this is an ongoing process, the tool will continue to scan the dark web for more leaked data or attack indicators so you can proactively mitigate threats as they’re discovered.
This article was written by Alex Zawalnyski, the Copy Manager at Expert Insights, who works alongside software experts to research, write, fact-check, and edit articles relating to B2B cyber security and technology solutions. This article has been technically reviewed by our technical researcher, Laura Iannini, who has experience with a range of cybersecurity platforms and conducts thorough product tests to ensure that Expert Insights’ reviews are definitive and insightful.
Research for this guide included:
- Conducting first-hand technical reviews and testing of several leading dark web monitoring providers
- Interviewing executives in the dark web monitoring space, as well as the wider Data Loss Prevention (DLP) industry, for first-hand insight into the challenges and strengths of different solutions
- Researching and demoing solutions in the dark web monitoring space and wider DLP security categories over several years
- Speaking to several organizations of all sizes about their dark web monitoring challenges and the features that are most useful to them
- Reading third-party and customer reviews from multiple outlets, including paid industry reports
This guide is updated at least every 3 months to review the vendors included and ensure that the features listed are up to date.
We recommend that all organizations consider implementing a solution that will help them identify and remediate data loss. This list has therefore been written with a broad audience in mind.
When considering dark web monitoring solutions, we evaluated providers based on the following criteria:
Features: Based on conversations with vendors, end customers, and our own testing, we selected the following key features:
- Threat hunting: Dark web monitoring tools should proactively hunt for stolen data, and threats and risks that affect your network.
- Wide visibility: Dark web monitoring platforms must provide broad visibility to give users the best chance of identifying their data and references to their company on forums, chatrooms, marketplaces, and messaging apps. Some tools in this Shortlist combine dark web monitoring with social media monitoring.
- Continuous monitoring: The platform should monitor the dark web 24/7 to identify its customer’s information as soon as possible. With attacks happening across the globe all the time, threat hunting cannot be limited to office hours.
- Analysis: The solution should have crawlers, scrapers, and scanners that analyze content and assess the risk to its customer’s business in real time. This may provide an understanding of how a data breach occurred or how one is likely to occur in the future.
- Actionable alerts: Dark web monitoring solutions should have an efficient way of alerting admins to any relevant updates. The alerts should convey as much information as possible, while enabling admins to react quickly.
- Reports: Dark web monitoring solutions should calculate a risk score that enables users to monitor the security of specific assets and implement more stringent security measures where relevant.
- Facilitated response: While not all dark web monitoring solutions have the capability to remediate threats from within the platform, at a minimum they should integrate with their customer’s wider security stack to facilitate and coordinate this response. Some solutions may be able to remove harmful content, but this is not the case for all products.
Market perception: We reviewed each vendor included on the Shortlist to ensure they are reliable, trusted providers in the market. We reviewed their documentation, third-party analyst reports, and—where possible—we have interviewed executives directly.
Customer usage: We use market share as a metric when comparing vendors and aim to represent both high market share vendors and challenger brands with innovative capabilities. We have spoken to end customers and reviewed customer case studies, testimonials, and end user reviews.
Product heritage: Finally, we have looked at where a product has come from in the market, including when companies were founded, their leadership team, their mission statements, and their successes. We have also considered product updates and how regularly new features are added. We have ensured all vendors are credible leaders with a solution we would be happy to use ourselves.
Based on our experience in the DLP and broader cybersecurity market, we have also considered several other factors, such as the benefit of consolidating multiple features into a single platform, the quality of the admin interface, the customer support on offer, and other use cases.
This list is designed to be a selection of the best dark web monitoring providers. Many leading solutions have not been included in this list, with no criticism intended.
 Written By
Written By
Alex is an experienced journalist and content editor. He researches, writes, factchecks and edits articles relating to B2B cyber security and technology solutions, working alongside software experts.
Alex was awarded a First Class MA (Hons) in English and Scottish Literature by the University of Edinburgh.
 Technical Review
Technical Review
Laura Iannini is a Cybersecurity Analyst at Expert Insights. With deep cybersecurity knowledge and strong research skills, she leads Expert Insights’ product testing team, conducting thorough tests of product features and in-depth industry analysis to ensure that Expert Insights’ product reviews are definitive and insightful.
Laura also carries out wider analysis of vendor landscapes and industry trends to inform Expert Insights’ enterprise cybersecurity buyers’ guides, covering topics such as security awareness training, cloud backup and recovery, email security, and network monitoring. Prior to working at Expert Insights, Laura worked as a Senior Information Security Engineer at Constant Edge, where she tested cybersecurity solutions, carried out product demos, and provided high-quality ongoing technical support.
Laura holds a Bachelor’s degree in Cybersecurity from the University of West Florida.