Every cybersecurity vendor claims to “enable zero trust,” but after the product demos and pitch decks, CISOs have the same question: where do we actually start?
CISA’s Zero Trust Maturity Model provides the architectural framework, but it was written as guidance for federal agencies, not as an IAM deployment plan, and the gap between the two is where most organizations stall. They understand it in theory, but they don’t know what to do to implement it on Monday morning.
We’ll map CISA’s five pillars to a phased IAM maturity model that gives security teams a starting point, a sequence, and a way to measure progress without trying to transform everything at once.
CISA’s Five Pillars and What They Mean for IAM
CISA’s Zero Trust Maturity Model organizes zero trust around five pillars. The table below maps each pillar to its practical IAM implication, showing what each one means for how identity is managed, verified, and enforced across the environment.
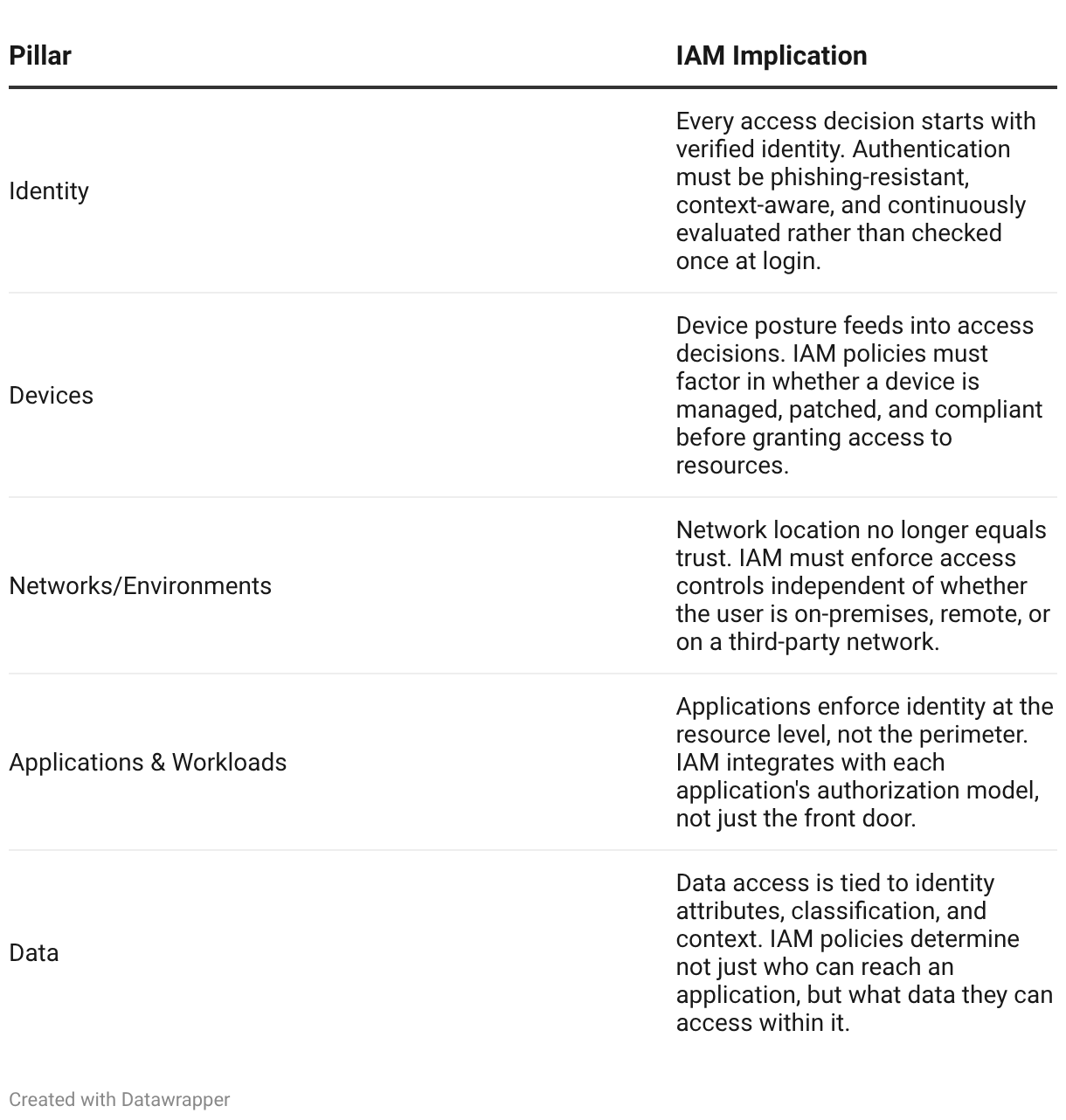
The critical shift across all five pillars is the same: trust is never inherited from the network. Every access request is evaluated on its own merits, and identity is the common thread that ties the decision together.
A Practical IAM Maturity Model
Mapping these pillars to a phased rollout gives teams a way to assess where they are today and what the next realistic step looks like. Four phases define the progression:
- Phase 1: Perimeter-dependent: Trust is based primarily on network location. Users inside the corporate network or VPN are treated as trusted. MFA coverage is partial or limited to VPN access. Identity governance is manual, with static group memberships and infrequent access reviews. Most organizations still have significant portions of their environment operating at this level.
- Phase 2: Foundation: MFA is enforced across all users and applications, not just VPN. A centralized identity provider handles authentication, and basic conditional access policies are in place, blocking access from non-compliant devices or unfamiliar locations. This is where the program delivers its first measurable risk reduction.
- Phase 3: Adaptive: Conditional access policies become risk-based rather than rule-based. Authentication strength adjusts dynamically based on context: device posture, sign-in risk score, resource sensitivity, and user behavior patterns. Automated provisioning and deprovisioning tie identity lifecycle to HR events, eliminating orphaned accounts.
- Phase 4: Continuous verification: Trust is evaluated throughout the session, not just at authentication. Session re-evaluation triggers step-up authentication when context changes mid-session, such as a device falling out of compliance or a user accessing a higher-sensitivity resource. Behavioral trust scoring provides continuous identity verification across all five CISA pillars, and access decisions are fully automated based on real-time risk signals.
Each phase builds on the one before it. Skipping phases, particularly jumping from Phase 1 to Phase 4, creates fragile implementations that collapse under the weight of exceptions.
Where to Start: Sequencing the First 90 Days
The biggest barrier to zero trust IAM implementation is not technology, it’s sequencing. Organizations that try to address all five CISA pillars simultaneously risk spreading their resources too thin, causing them to lose momentum before any single pillar reaches maturity.
Identity inventory and gap analysis is the universal first step. You cannot enforce zero trust policies on accounts you do not know exist, so it’s important to map every identity source (including cloud directories, on-premises Active Directory, service accounts, and third-party contractor access) and identify where gaps in visibility exist. This inventory becomes the foundation for every policy decision that follows.
MFA enforcement is the highest-impact quick win. Phishing-resistant MFA, specifically FIDO2 security keys or passkeys, deployed across all user accounts closes the single largest attack vector in most environments. This is the move that takes an organization from Phase 1 to Phase 2, and it delivers measurable risk reduction faster than any other zero trust initiative.
Conditional access baseline comes next. Start with broad policies that block access from non-compliant devices and unrecognized locations, then refine based on the false positive patterns that emerge. The goal in the first 90 days is not to build a sophisticated risk-adaptive engine; it is actually to establish the policy framework that the engine will eventually run on.
What Continuous Verification Actually Looks Like
Continuous identity verification is the most misunderstood concept in zero trust. It does not mean re-prompting users for their password every few minutes. It means the system is constantly re-evaluating whether the conditions that justified the original access decision still hold true.
In practice, this plays out as session-level trust assessment. A user authenticates in the morning from a managed laptop in a recognized location. Two hours later, the device fails a compliance check because a critical patch is overdue. In a perimeter-based model, the user’s session continues uninterrupted. In a continuous verification model, the IAM platform detects the posture change and responds, either by limiting access to lower-sensitivity resources or by requiring step-up authentication before allowing the session to continue.
The same logic applies when a user’s behavior deviates from their baseline. If an account that normally accesses three applications suddenly begins enumerating resources across the environment, continuous verification treats that as a trust signal that warrants re-evaluation, rather than treating it as normal activity that was already authorized at login.
Common Stall Points
Even with a clear maturity model and a sequenced roadmap, zero trust IAM programs lose momentum. These are the patterns that most commonly cause stalls, and most of them have nothing to do with technology.
- Treating zero trust as a product purchase: Zero trust is an architecture model, not a SKU. Organizations that expect a single vendor deployment to “achieve zero trust” stall at Phase 2 when they realize the remaining work is policy design, process change, and cross-team coordination.
- Legacy application exceptions that never get addressed: Every environment has applications that don’t support modern authentication. The risk isn’t in granting temporary exceptions. It’s in letting those exceptions become permanent, creating a growing shadow perimeter that undermines the zero trust posture.
- Executive buy-in dropping off after Phase 1: MFA rollout is visible and measurable, which makes it easy to fund. The adaptive and continuous verification phases are harder to quantify, and budget approval slows unless security teams tie each phase to specific risk reduction metrics.
- Scope creep across all five pillars at once: CISA’s model covers identity, device, network, application, and data. Trying to mature all five simultaneously dilutes focus. Organizations that reach Phase 4 do so by sequencing: identity first, then device posture, then expanding outward.
Final Thoughts
Zero trust is a direction, not a destination, and the IAM maturity model gives teams a way to measure how far they’ve traveled.
The organizations that make real progress treat it as a multi-phase architecture shift rather than a single project with a completion date. They start with identity inventory and MFA, build toward adaptive access, and use continuous identity verification as the north star rather than the starting line.
The framework exists. The question is no longer “what is zero trust?” It is “what phase are we in, and what does the next one require?”

