Market leading authentication with a variety of customization options and few drawbacks.

Overall, Cisco Duo Security is a very strong authentication solution which helps to significantly increase account and credential security. There are several powerful security features included, with easy yet granular controls that provide both less overhead for admins, and a more seamless login experience for end-users.
Duo’s multi-factor authentication is extremely quick and easy to use from an end-user perspective. A common weakness of multi-factor authentication options is that they can be cumbersome for end-users, but Duo offers an elegant, intuitive platform, with multiple options for authentication, including push notifications through an authenticator app, text message SMS codes, security keys and more.
Duo sends push notifications through its own “Duo Push” mobile app, which works similarly to other major authentication apps end users will be used to using. Administrators can send end users the link to download this app on Android and iOS devices when they enroll a mobile device.
Duo also showcases useful information within the authenticator application about account access attempts, including the IP address and location of the person trying to log in. This can be very useful for end users, helping them to verify which login attempts are genuine, and which are potentially malicious.
As part of Duo’s authentication process, the system also tracks which operating systems and browsers are being used to access corporate accounts, along with which versions of these platforms are being used, creating a baseline of user behavior and can then flagging unusual account activity, such as login attempts from new devices, new locations, or unusual times.
This allows Duo to monitor if a device or browser is out of date or running an operating system that has security vulnerabilities. Admins can set highly granular policies which govern whether these devices are allowed to access corporate accounts, or if users need to run an update before they can gain access. This is a highly effective security tool to prevent vulnerable devices from accessing to sensitive data.
Duo also offers granular access controls specifically for mobile devices. Admins can freely control which operating systems, browsers and plugins are allowed to access corporate accounts, and are able to block devices running out of date operating systems. If a user tries to log in using a device that is out of date, Duo notifies them upon attempted login, with clear instructions on how to update their device.
Duo features secure single sign-on that provides users seamless access to all of their applications with just one set of credentials. Duo integrates with all on-premises active directory solutions, as well as Microsoft Azure, Google, Okta and other SAML 2.0 identity providers. After performing an integration with a particular solution, Duo will automate the SAML attribute names, which means that future integrations will be faster.
Deploying SSO is very straightforward, and only takes around five minutes.
Duo provides granular options for admin policies to govern access to secure accounts. There are three types of policies available: Global, Application and Group. Global policies apply to every user and application, Application policies can be applied to specific apps, to provide a higher level of security where needed. Multiple group policies can be configured per application and can be given different priority levels.
Policies can configure the following:
The huge variety of options when it comes to policy management means that configuring Duo can initially feel overwhelming. However, there is clear and concise documentation around configuring policies, which is linked to in the policy management menus in the admin console.
Overall, access policies are a very strong feature in this solution, and the high level of customization options available in the admin portal allows admins to set extremely specific security rules.
Duo Trust Monitor is a threat detection feature that highlights valuable and actionable security events, to help you better manage the security of your organization. Within the admin console, the “Risk Profile” settings allow admins to set security policies for the following use cases:
The Security Events page provides an overview of any security incidents based on a specific Risk Profile. This can help administrators view patterns of activity that would otherwise be difficult to detect.
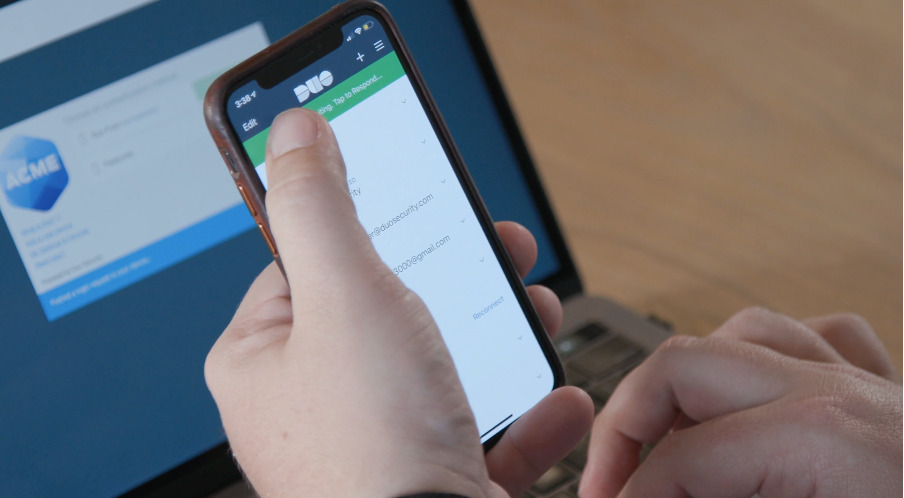
Accepting a login request with Duo
Duo is very easy to deploy. The solution can be ready in hours, or minutes, depending on the level of specific integrations and policy configurations required. This is a major benefit of the Duo service, as often security solutions can take days to deploy, but Duo packs a lot of features and functionality into an easily configured service.
Deploying Duo to applications can look intimidating at first, but Duo provides links to high quality documentation throughout the admin panel. Administrators should not run into significant issues if they follow these instructions and, in a worst-case scenario, Duo has plenty of support available to assist with deployment.
Duo’s admin dashboard is intuitive, with a modern look and feel. There are a few instances where information is cluttered, mostly around lists or policy options, but for the most part the dashboard is easy to navigate and use.
The dashboard provides an easy-to-understand overview of the following:
How many users are locked out of Duo (from failed login attempts), how many users can bypass authentication, and how many are inactive Number of users, licenses, admins, groups, devices, and new security events Graph of how many authentications have happened in the last 48 hours Detailed authentication log Almost every page on Duo Access that contains data also contains some type of corresponding graph, and reports can be easily accessed and generated.
In general, it’s very easy for end users to authenticate access with Duo. There are several available authentication options, including biometric authentication with fingerprint scanning on smartphones, and facial recognition on iOS devices. There is a full guide to Duo’s biometric options here. It’s also very easy for users to create their own accounts.
However, something to be aware of is that, if someone is using their smartphone to authenticate, it is possible to be locked out of accessing essential work functions if the phone is lost or stolen. This means there can be some lost time and productivity while admins reset account access for users. This issue is not unique to Duo, but it is an unavoidable aspect of implementing an authentication solution, and something that admins should be aware of.
Duo helps to mitigate against this issue by allowing users to have multiple devices, which the user can configure themselves. This means if one is lost or stolen, another device can be used to authenticate in it’s place. This works as a good compromise between maintaining security, while reducing the risk of loss of productivity that comes from being locked out of accounts.

Duo's admin dashboard
Overall, the deployment process is easy to manage, with plenty of high-quality documentation and support available for organizations to help make the deployment process easier.
Users can be onboarded from active directory services such as Microsoft Azure, on-premise AD or LDAP, via CSV files, or can be manually added by admins. There is also a self-remediation feature, which can help to reduce the burden on IT staff; users can create accounts and choose their own authentication methods in just a few minutes. Admins can send out activation links to users’ devices at any time if needed.
It’s also very easy to remove someone from the Duo platform. In the case of an employee leaving the organization, for example, admins can configure the service to automatically deny that user access to any corporate accounts (even when the username and password is known) which is an important security benefit. If users added via integration with third-party active directory services, like Microsoft Azure, are removed, or have group memberships changed, in the source directory, their access to Duo is also automatically revoked.
On the flipside, admins can also allow certain users to bypass authentication entirely, a feature that should be used with caution by admins.
One of Duo’s major strengths is its number of prebuilt integrations. Duo can integrate 2FA and SSO with over 120 applications. These include—but are not limited to—Microsoft O365, Slack, Zoom, Freshdesk, DocuSign, and more. You can view their full list of integrations here.
Duo also supports generic integration for any application that uses LDAP, RADIUS, or SAML standards. LDAP and RADIUS configurations require that users are created in advance instead of being self-enrolled, in most cases. There are six exceptions to this: Array Networks, Citrix, Barracuda, F5BigIP, Sonicwall, Juniper, which all support web-based enrolment. Duo recommends the use of directory sync for all integrations however, as it is the most secure method of onboarding.
The ability to implement Duo with applications not specifically listed in Duo further increases its versatility and gives admins more flexibility in configuring the service.
Duo’s Web v4 SDK also allows admins to integrate Duo’s 2FA with their own web applications. This library is available in Python, Java, and PHP. For other programming languages, Duo’s OIDC Auth API is also available. This API can be used to integrate 2FA with homegrown applications, even if they are not completely web-based
You can read documentation about Duo’s integration standards here:
Duo Enrollment
Customer support is available over email or the phone. Their typical support times are between 9am-5pm during the week, with a 24/7 support option for emergency use. Duo also offers a premium support option, Duo Care, which provides 24/7 coverage 365 days a year, but this option has an additional cost above the Duo Access pricing.
Duo provides global support, with different phone numbers for specific countries. Duo promises to respond to critical issues in just one business hour, while high severity issues will take up to two business hours. Low severity issues will typically receive a response in one business day.
During our trial period with the product, a support engineer from the Duo team reached out unprompted to offer help and assistance with the product, which exemplified the high level of customer support offered by Duo and was a pleasant surprise for our technical review team.
Duo provides extensive support documentation with useful information and guides on deployments, policies and controls, device insights, admin roles, device health and much, more. The support is very easy to find; every page on Duo Access has a sidebar with links to all available support documentation.
Duo also provides how-to videos in their support documentation, which is very useful for quickly seeing the steps needed to configure an integration or implement a particular feature.
At times, the documentation can get lengthy and complex, which is unavoidable with a complex security product. But Duo has broken down documentation into easy steps whenever possible.
Duo’s service level agreements (SLAs) can be found in their legal page here: https://duo.com/legal/sla.
Duo guarantees 99.9% uptime during any calendar month (with a few exceptions.) Otherwise, customers are eligible to request a Service Credit for the downtime.

Duo's authentication page
Duo is available in four different packages. Duo Free is a free version of the service, available for up to 10 users. This solution provides MFA for iOS and Android devices, MFA with security teams, OTPs and hardware tokens, and unlimited integrations.
The next package service up from Duo Free is Duo MFA, which comes in at $3.00 USD per user per month. This provides all User Trust features, which covers MFA, telephony, and user self-enrolment. It also provides a dashboard of connected devices, security policies and secure single sign-on, with unlimited integrations.
Duo Access is the third option available, which allows organizations detect when a device is making a risky connection, monitor how up to date the devices used across the organization are, and encourage end users to correct if their devices have security issues.
Access offers all user trust and most device trust features (bar corporate devices), specific policies and anti-virus checking, almost all adaptive authentication to features, and all single sign-on features, aside from those related to the Duo Network Gateway. Duo Access is priced at $6.00 USD per user per month and is our recommended Duo package for most organizations.
Finally, Duo Beyond is an enterprise-focused option, which is priced at $9 per user, per month. Duo Beyond provides all Duo features, including the enterprise corporate device policies, endpoint management integrations, and the Duo Network Gateway, which allows organizations to secure access to internal web applications.
Overall, Duo Access is a very strong authentication solution which helps to significantly increase account and credential security. There are several powerful security features included, with easy yet granular controls that provide both less overhead for admins, and a more seamless login experience for end-users.
The biggest strength of the Duo Access platform is the level of customization and granularity that can be achieved, without a complex setup or any messy admin configurations. The multi-factor authentication is extremely fast and easy, and the fact admins can gain full visibility of corporate devices, their security scores, and which accounts they are accessing, is a highlight of this service over competitors in the MFA space.
We would highly recommend Duo Access as a strong option for organizations looking to implement MFA and SSO—especially those that want to utilize Bring Your Own Device policies. Duo is a trusted solution that is easy to deploy, straightforward to configure, and provides confidence and security that accounts are protected, while empowering employees to access accounts when needed.
Tested by: Laura Iannini
User Authentication
duo.com
2010
Ann Arbor, MI
Cloud
SMBs, Enterprise







